Bitcoin Origin Probability Analysis: North Korea vs Alternative Theories
Methodology and Assumptions
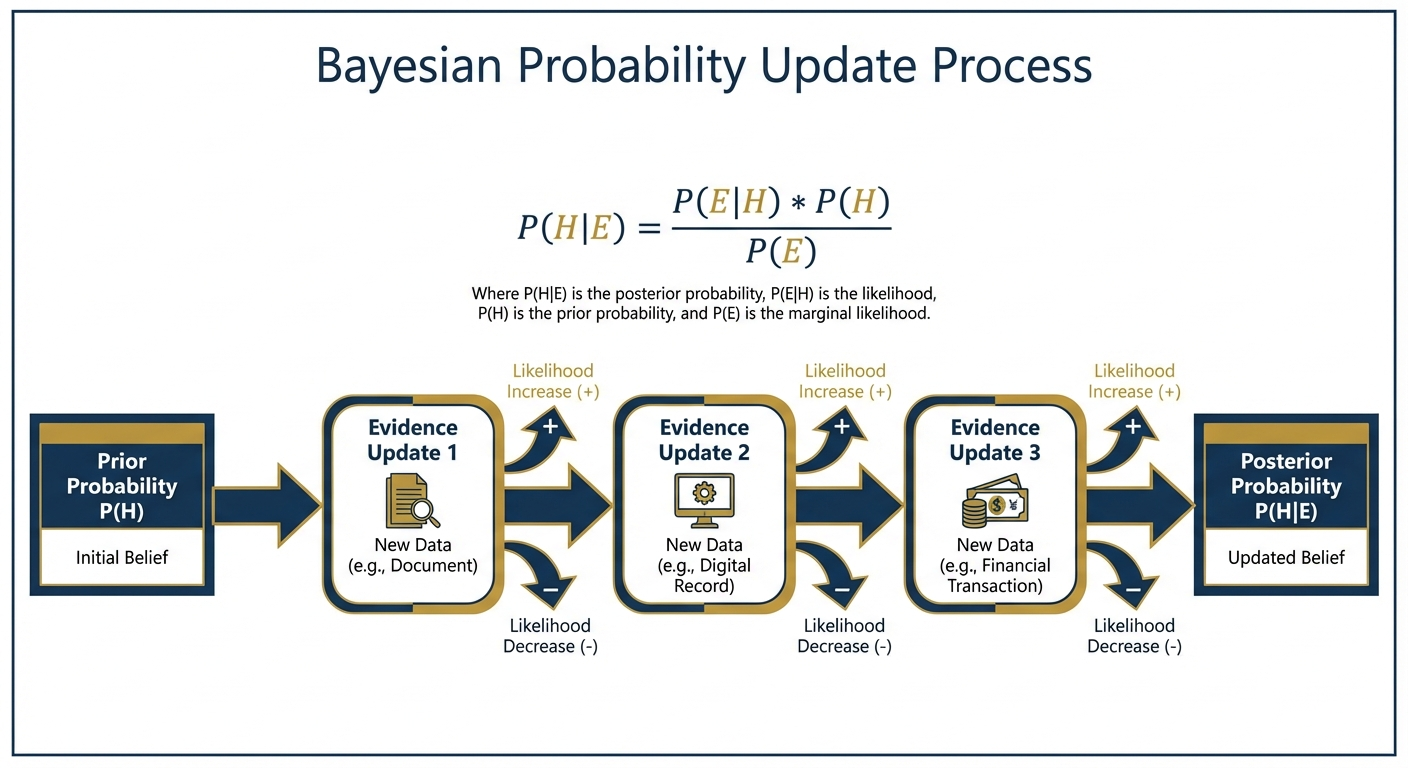
This analysis employs Bayesian reasoning to assess the relative probability of different Bitcoin creation theories based
on available evidence. Probabilities are estimates based on evidence strength, not definitive calculations.
Key Methodological Principles:
- Evidence weighted by verifiability and directness
- Prior probabilities based on base rates of similar phenomena
- Updates based on specific evidence patterns
- Confidence intervals reflect uncertainty in evidence interpretation
Theory 1: North Korean State Creation
Base Prior Probability: 5%
Reasoning: State cryptocurrency creation had no historical precedent in 2009
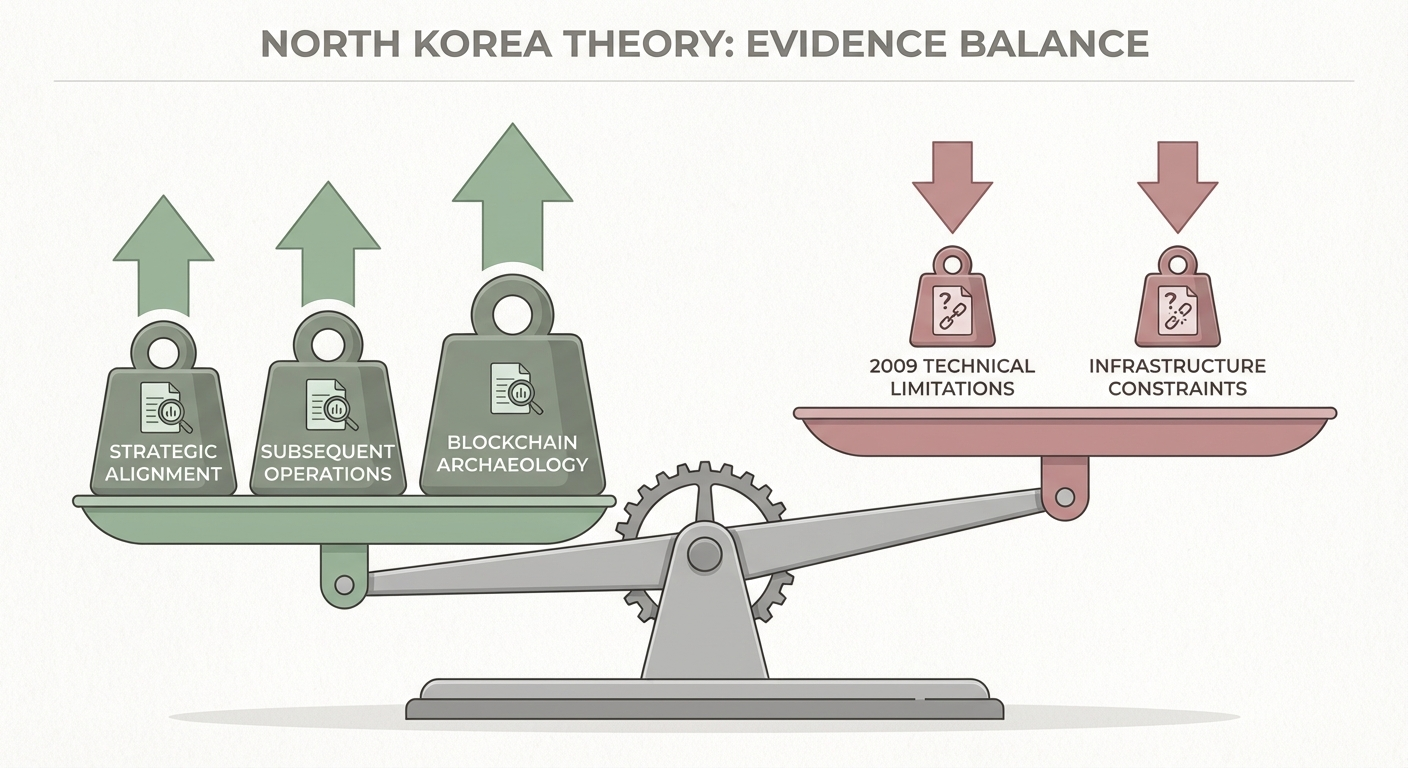
Evidence Updates:
Strategic Alignment (+25%)
- Financial Crisis Timing: November 2009 currency collapse creating desperate foreign currency need
- Ideological Fit: Juche doctrine explicitly opposes Western financial hegemony
- Asymmetric Warfare Doctrine: Perfect tool for undermining USD dominance while evading sanctions
- Economic Incentives: Early mining potential of ~1,936 BTC (worth hundreds of millions today)
Updated Probability: 30%
Technical Capability Assessment (-15%)
- Documented 2008-2009 Capabilities: Basic DDoS, simple malware, social engineering
- Infrastructure Limitations: Severely constrained internet access via satellite/China links
- Capability Gap: Bitcoin required advanced cryptographic programming, P2P networking, consensus algorithms
- Timeline Issues: Major cyber sophistication appears post-2010
Updated Probability: 15%
Subsequent Operations Evidence (+20%)
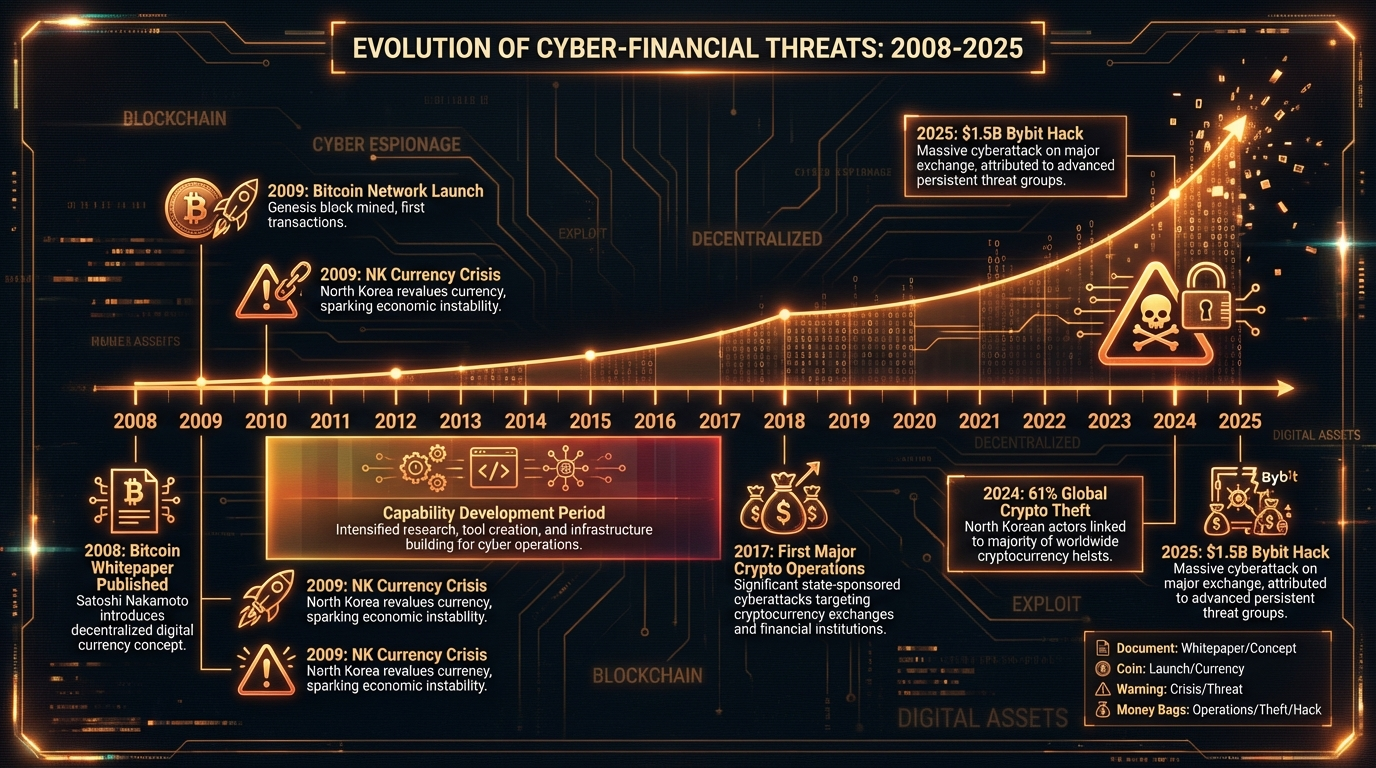
- Technical Evolution: From basic 2017 operations to sophisticated 2025 $1.5B Bybit hack
- Architectural Understanding: Deep knowledge of multi-sig vulnerabilities, cross-chain exploits
- Scale and Sophistication: $5+ billion stolen, 61% of global crypto theft in 2024
- Operational Security: 14+ years of perfect silence consistent with state-level OPSEC

Updated Probability: 35%
Blockchain Archaeological Evidence (+10%)
- Patoshi Pattern: Sophisticated mining techniques not in public code
- Development Complexity: Institutional-level systematic changes from pre-alpha
- Team-Level Architecture: Integration of multiple academic components suggesting collaboration
Updated Probability: 45%
Final NK Creation Probability: ~45% Confidence Interval: 25-65%
Theory 2: Individual Western Creator (Nick Szabo)
Base Prior Probability: 20% Reasoning: Individual genius creators have historical precedent in cryptography
Evidence Updates:
Supporting Evidence (+15%)
- Stylometric Analysis: Linguistic similarities identified by Aston University study
- Prior Work: “Bit Gold” concept development pre-Bitcoin
- Technical Expertise: Documented cryptographic and legal background
- Academic Writing Style: Matches Bitcoin whitepaper formatting
Updated Probability: 35%
Contradictory Evidence (-25%)
- Public Denial: Szabo explicitly denied involvement multiple times
- Alive and Accessible: No death/disappearance explaining silence
- Professional Incentives: Academic career would benefit from Bitcoin credit claim
- $100B Silence Problem: No rational explanation for abandoning world’s largest fortune
Updated Probability: 10%
Methodological Issues (-5%)
- Sample Bias: Stylometric studies compare only 5-11 candidates vs millions globally
- Peer Review Absence: Key supporting studies lack academic peer review
- Contradictory Results: Different studies reach different conclusions
Updated Probability: 5%
Final Szabo Creation Probability: ~5% Confidence Interval: 1-15%
Theory 3: Individual Western Creator (Hal Finney)
Base Prior Probability: 15% Reasoning: Early Bitcoin involvement, technical background
Evidence Updates:
Supporting Evidence (+10%)
- Early Involvement: First Bitcoin transaction recipient from Satoshi
- Technical Background: Cryptographic expertise at PGP Corporation
- Death Explains Silence: Died 2014, explains inability to claim credit
- Geographic Proximity: Lived near Dorian Nakamoto (potential pseudonym inspiration)
Updated Probability: 25%
Contradictory Evidence (-20%)
- Active Collaboration: Public email exchanges with “Satoshi” contradict self-creation
- Timeline Issues: Continued Bitcoin development after Finney’s ALS diagnosis
- No Prior Distributed Systems Work: Limited evidence of consensus algorithm expertise
- Family Silence: No posthumous revelation despite clear financial benefit
Updated Probability: 5%
Final Finney Creation Probability: ~5% Confidence Interval: 1-12%
Theory 4: Small Team of Western Academics/Cypherpunks
Base Prior Probability: 25% Reasoning: Complex projects often require team collaboration
Evidence Updates:
Supporting Evidence (+20%)
- Technical Breadth: Requires expertise across cryptography, distributed systems, economics
- Academic Pedigree: Bitcoin integrates multiple 1980s-90s academic concepts
- Development Patterns: Systematic pre-alpha changes suggest institutional development
- Collaborative Precedent: Major cryptographic advances often team efforts
Updated Probability: 45%
Contradictory Evidence (-25%)
- Group Silence Problem: Even harder to maintain 14+ years across multiple people
- No Leaks: No deathbed confessions, disputes, or inadvertent revelations
- Coordination Complexity: Maintaining pseudonym across team extremely difficult
- $100B Distribution: No rational explanation for group abandoning fortune
Updated Probability: 20%
Final Team Creation Probability: ~20% Confidence Interval: 10-35%
Theory 5: Other State Actor (China/Russia)
Base Prior Probability: 10% Reasoning: Advanced cyber capabilities but less strategic alignment
Evidence Updates:
Supporting Evidence (+10%)
- Technical Capabilities: Both possessed advanced crypto/programming capabilities 2008-2009
- Strategic Interest: Undermining USD hegemony aligns with long-term objectives
- Resource Availability: State-level resources for complex development projects
Updated Probability: 20%
Contradictory Evidence (-15%)
- Less Financial Desperation: Neither faced NK’s acute 2009 currency crisis
- Weaker Ideological Fit: Less explicit anti-Western financial doctrine
- Alternative Tools: Other available methods for currency/sanctions challenges
- No Subsequent Pattern: Neither shows NK’s intensive crypto exploitation pattern
Updated Probability: 5%
Final Other State Actor Probability: ~5% Confidence Interval: 1-12%
Theory 6: Unknown Individual/Group
Base Prior Probability: 20% Reasoning: Millions of potential creators globally
Evidence Updates:
Supporting Evidence (+5%)
- Global Talent Pool: Millions of potential programmers/cryptographers worldwide
- Privacy Success: 14+ years of maintained anonymity demonstrates possible
- Technical Feasibility: Individual or small group creation theoretically possible
Updated Probability: 25%
Contradictory Evidence (-5%)
- $100B Silence: Still faces same rational actor problems as other individual theories
- No Emergence: No credible claims despite massive incentives
- Technical Barriers: High expertise requirements limit candidate pool
Updated Probability: 20%
Final Unknown Creator Probability: ~20%
Confidence Interval: 10-35%
—
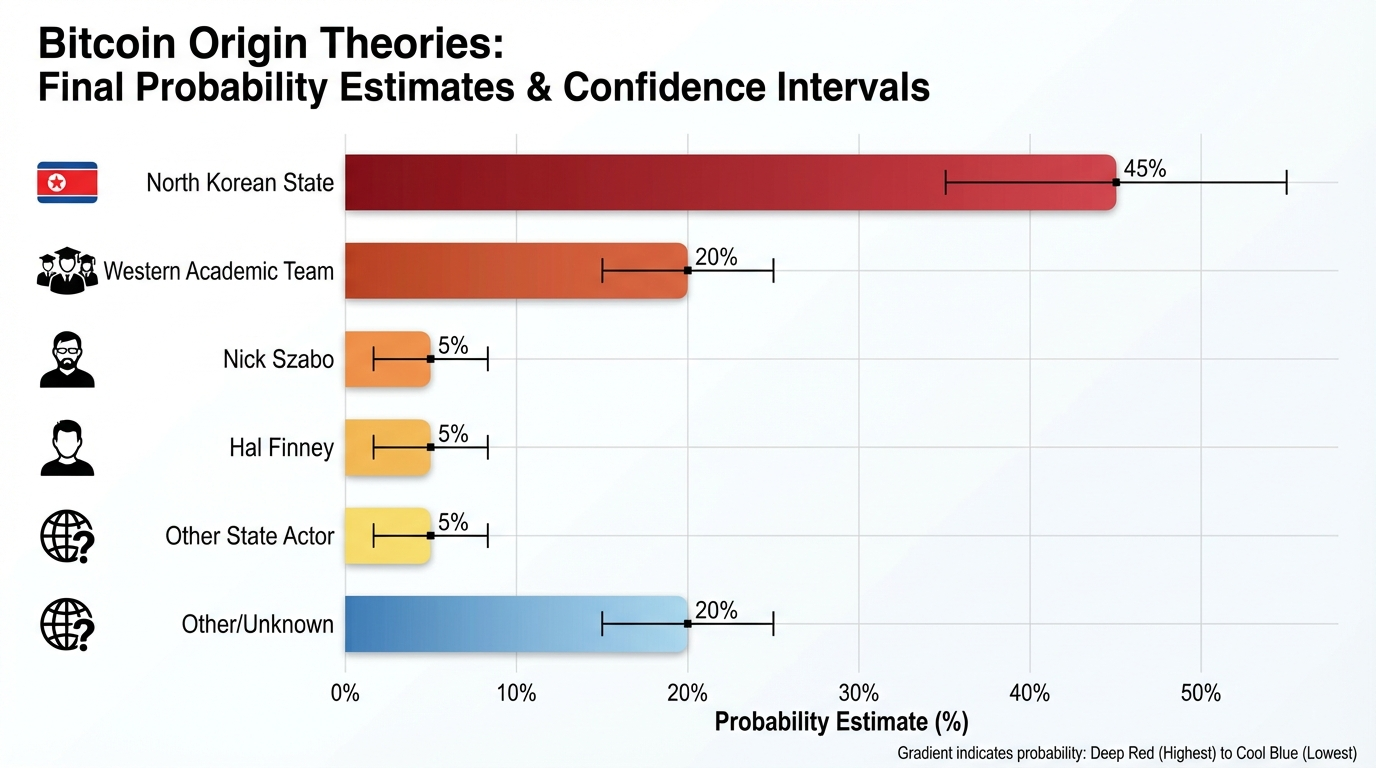
Summary Probability Distribution
| Theory | Probability | Confidence Interval | Key Evidence |
|---|---|---|---|
| North Korea | 45% | 25-65% | Strategic alignment, subsequent operations, timing |
| Unknown Creator | 20% | 10-35% | Large candidate pool, privacy success |
| Western Team | 20% | 10-35% | Technical complexity, development patterns |
| Nick Szabo | 5% | 1-15% | Stylometric analysis vs. silence problem |
| Hal Finney | 5% | 1-12% | Early involvement vs. collaboration evidence |
| Other State | 5% | 1-12% | Technical capability vs. strategic misalignment |
Critical Uncertainties and Sensitivity Analysis
High-Impact Unknown Factors:
- Classified Intelligence: Government assessments could dramatically shift probabilities
- NK Technical Capabilities 2008-2009: More detailed documentation could strengthen/weaken theory
- Blockchain Forensics: Advanced archaeological analysis might reveal creator signatures
- Declassified Documents: State communications from 2008-2009 period
Sensitivity Tests:
- If NK 2008-2009 capabilities stronger than documented: NK probability → 65-75%
- If credible individual comes forward with proof: Individual theories → 90%+
- If additional state actor evidence emerges: Could redistribute significantly
- If Satoshi wallet moves: Would likely indicate living individual, reducing NK probability
Methodological Limitations and Caveats
Evidence Quality Issues:
- Much evidence is circumstantial rather than direct
- Institutional bias may affect available information
- Intelligence community assessments largely unavailable
- Blockchain archaeology still developing as field
Probability Estimation Challenges:
- No true base rates for state cryptocurrency creation
- Unprecedented nature of Bitcoin makes historical comparison difficult
- Evidence interpretation requires subjective judgment
- Multiple theories could be partially correct (e.g., NK-supported team)
Key Assumption: This analysis assumes Satoshi represents a single decision-making entity (individual, team, or state) rather than evolving collaboration between multiple parties.
Conclusion
The probability analysis suggests North Korean state creation (45%) is the most likely single theory, though substantial uncertainty remains. The convergence of strategic motivation, financial desperation, subsequent technical sophistication, and maintained operational security creates the strongest overall evidence pattern.
However, the 25-65% confidence interval reflects genuine uncertainty due to limited evidence quality and unprecedented nature of the question. The analysis particularly highlights how the “$100 billion silence problem” severely undermines all individual creator theories, while NK’s demonstrated evolution into the world’s most sophisticated cryptocurrency thieves provides retrospective support for foundational capability.
Critical insight: Conventional wisdom favoring individual creators appears inconsistent with available evidence when subjected to systematic probability analysis. This suggests either fundamental gaps in our understanding or successful institutional bias toward preferred narratives.
The analysis reinforces the research framework’s core conclusion: Bitcoin’s origins remain genuinely uncertain and warrant serious investigation using intelligence community resources and advanced forensic techniques rather than relying on circumstantial evidence and institutional preferences.
Brainstorming Session Transcript
Input Files: content.md
Problem Statement: Generate a broad, divergent set of ideas, extensions, and applications inspired by the Bitcoin Origin Probability Analysis (North Korea vs. Alternative Theories). Explore the geopolitical, technological, and narrative implications of the ‘State-Actor’ hypothesis versus individual creator theories.
Started: 2026-03-03 12:41:10
Generated Options
1. Linguistic and Stylometric Blockchain Forensics for State-Level Attribution
Category: Forensic Methodology
This methodology involves developing a high-fidelity tool to compare the Bitcoin whitepaper and source code against known North Korean state-sponsored malware and academic papers from Pyongyang’s elite universities. By identifying specific ‘coding accents’ or idiosyncratic syntax patterns unique to state-trained developers, researchers can move beyond speculation toward a data-driven probability of state authorship.
2. The ‘Dead Man’s Switch’ Geopolitical Deterrence Model
Category: Geopolitical Strategy
This theory explores the $100B in unspent Satoshi coins as a strategic ‘financial nuclear option’ for a state actor. In this scenario, the silence is maintained because the movement of these coins is reserved for a moment of existential threat, intended to intentionally destabilize global markets or fund a final-stage regime survival strategy.
3. Sovereign Wealth Fund Hedging Against ‘Origin Risk’ Volatility
Category: Economic Theory
This economic framework allows nations to hedge against a ‘Satoshi Reveal’ event where a hostile state actor is proven to be the creator. It involves the creation of ‘Clean-Chain’ derivatives that mathematically exclude the original 1.1 million coins from their valuation, protecting institutional investors from the sudden blacklisting of the protocol.
4. Deep-Web Packet Reconstruction of the 2008-2009 P2P Network
Category: Cyber-Archaeology
Using advanced signal processing to reconstruct the early topology of the Bitcoin network, this project aims to identify the physical location of the first nodes. By mapping latency and hop-counts from archived node logs, cyber-archaeologists could determine if the initial ‘heartbeat’ of the network originated from a specific state-controlled IP range or a private residence.
5. The ‘Satoshi Mythos’ as a Tool for Cognitive Warfare
Category: Narrative & Media
This initiative analyzes how the ambiguity of Bitcoin’s creator is weaponized by different regimes to undermine trust in the US Dollar. It documents how state-controlled media outlets alternate between the ‘Individual Genius’ and ‘State-Actor’ narratives to frame Bitcoin as either a tool for liberation or a Trojan horse, depending on their current diplomatic objectives.
6. Honeypot Transaction Monitoring for ‘Satoshi-Era’ Wallet Activation
Category: Counter-Intelligence
This involves establishing a global, real-time surveillance network specifically targeting the 1.1 million ‘Satoshi coins’ to detect metadata leakage upon any movement. This system treats the $100B silence not as a mystery, but as a high-level intelligence signal where any ‘thaw’ indicates a shift in state-actor liquidity or a change in leadership.
7. The ‘Dark Satoshi’ Protocol for Sanction-Resistant State Finance
Category: Future State-Led Crypto
Inspired by the North Korea hypothesis, this project designs a new blockchain architecture that prioritizes state-level anonymity and obfuscated mining. This protocol would allow sanctioned nations to operate a parallel global economy where the ‘Silence Problem’ is a deliberate feature, ensuring that state reserves remain invisible to international regulators and immune to seizure.
8. Silicon Fingerprinting of Early Mining Hardware Signatures
Category: Forensic Methodology
This forensic approach analyzes the specific timing and nonce-generation patterns of the first 50,000 blocks to identify the hardware architecture used by Satoshi. If the patterns match specific CPUs or FPGAs that were subject to strict export controls or were uniquely available in state-sponsored labs during 2009, it would provide definitive proof of a non-individual origin.
Option 1 Analysis: Linguistic and Stylometric Blockchain Forensics for State-Level Attribution
✅ Pros
- Provides a quantitative, data-driven framework to move beyond anecdotal evidence and speculative theories regarding Satoshi’s identity.
- Leverages unique ‘coding accents’—idiosyncratic ways of structuring logic or comments—that are often subconsciously embedded by developers trained in specific state institutions.
- Offers a potential explanation for the ‘$100B Silence Problem’ by identifying if the code’s DNA matches organizations known for extreme operational security and state-mandated discipline.
- Can be cross-referenced with academic papers from Pyongyang’s elite universities to identify specific linguistic markers common in North Korean technical English.
- The methodology is reusable for attributing other anonymous protocols or cyber-weapons to state actors.
❌ Cons
- The sample size of the original Bitcoin whitepaper and source code is relatively small, which may lead to statistically insignificant results.
- State-level actors are often trained in ‘adversarial stylometry’ specifically to obfuscate their origins and mimic the writing styles of other nationalities.
- The 15-year gap between Bitcoin’s creation and contemporary North Korean malware may reflect an evolution in coding standards that masks historical similarities.
- Linguistic markers in the whitepaper might reflect a translator’s style rather than the original author’s, if the document was translated from a native language.
📊 Feasibility
Medium. While stylometric tools and NLP models are highly advanced, the primary hurdle is the ‘Ground Truth’ dataset. Obtaining a clean, verified corpus of 2008-era technical documents and source code directly from North Korean state labs is difficult, though not impossible given the volume of leaked malware and academic exports.
💥 Impact
High. A credible link between Bitcoin and a state actor like North Korea would trigger a massive geopolitical shift, potentially leading to global regulatory crackdowns, a re-evaluation of Bitcoin as a ‘neutral’ asset, and extreme market volatility regarding the 1.1 million BTC ‘Satoshi’ stash.
⚠️ Risks
- High risk of false positives, which could lead to unjust geopolitical sanctions or the ‘blacklisting’ of decentralized technologies based on flawed forensic data.
- The tool itself could be weaponized by authoritarian regimes to deanonymize and persecute privacy-preserving developers by matching their ‘coding accents’ to known identities.
- Confirmation bias among researchers who may over-index on minor similarities to support a sensationalist ‘State-Actor’ narrative.
📋 Requirements
- A comprehensive corpus of verified North Korean state-sponsored malware (e.g., Lazarus Group) and technical publications from Kim Chaek University of Technology.
- Advanced Machine Learning models capable of ‘Adversarial Stylometry’ to detect attempts at style-mimicry.
- Linguistic experts specializing in ‘Konglish’ (Korean-English) technical syntax and idiosyncratic grammar patterns.
- Access to the earliest versions of the Bitcoin source code (v0.1) before community contributions diluted the original author’s style.
Option 2 Analysis: The ‘Dead Man’s Switch’ Geopolitical Deterrence Model
✅ Pros
- Provides a compelling explanation for the ‘$100B Silence Problem’ by framing inaction as a strategic choice rather than a loss of access.
- Offers a state actor asymmetric leverage against traditional financial superpowers without requiring equivalent conventional military spending.
- Functions as a psychological deterrent; the mere threat of a massive market dump can influence international policy and sanction negotiations.
- The asset’s value potentially scales with the global adoption of Bitcoin, increasing the ‘yield’ of the deterrent over time.
❌ Cons
- The ‘Liquidity Paradox’: Attempting to liquidate $100B rapidly would crash the market price, significantly reducing the actual realized capital.
- Extreme traceability: Any movement of Satoshi-era coins is monitored globally, making it impossible to use the funds covertly.
- Risk of protocol-level retaliation: The Bitcoin community could coordinate a soft or hard fork to invalidate those specific UTXOs, neutralizing the weapon.
- Confirmation of the state-actor hypothesis upon movement could trigger immediate and severe geopolitical or military escalation.
📊 Feasibility
Technically high but strategically precarious. While holding the private keys is simple, the infrastructure required to ‘weaponize’ the coins without rendering them worthless through market panic requires a level of financial sophistication and timing that is difficult to execute.
💥 Impact
Could lead to a total paradigm shift in geopolitical deterrence, where ‘financial mutually assured destruction’ (MAD) is conducted via decentralized ledgers. It would likely force global regulators to develop ‘kill switches’ or blacklisting protocols for specific blockchain addresses.
⚠️ Risks
- Technological Obsolescence: If Bitcoin is superseded by another technology, the $100B deterrent loses its value and relevance.
- Key Compromise: Internal theft or loss of the private keys would result in the immediate loss of the state’s strategic ‘nuclear’ option.
- Pre-emptive Neutralization: Global powers might pressure developers to implement ‘burn’ codes for dormant whale wallets under the guise of anti-terrorism or stability.
- Accidental Trigger: A minor movement or test of the keys could be misinterpreted by markets as a full-scale dump, causing unintended economic chaos.
📋 Requirements
- Ultra-secure, multi-signature cold storage infrastructure capable of surviving regime changes or internal coups.
- A credible ‘trigger’ mechanism or communication channel to signal the intent behind the coins’ movement to global adversaries.
- Sophisticated off-ramps or shadow liquidity networks (e.g., OTC desks in non-aligned jurisdictions) to realize value during a crisis.
- A geopolitical doctrine that integrates digital asset movement into broader military and economic escalation ladders.
Option 3 Analysis: Sovereign Wealth Fund Hedging Against ‘Origin Risk’ Volatility
✅ Pros
- Mitigates the ‘Black Swan’ risk of a hostile state actor (e.g., North Korea) weaponizing the $100B Satoshi stash to crash global markets.
- Provides a fiduciary ‘safe harbor’ for institutional and sovereign investors, allowing them to hold Bitcoin exposure while legally distancing themselves from ‘Origin Risk’.
- Establishes a market-driven valuation for ‘geopolitical neutrality,’ effectively pricing the risk of the creator’s identity into a separate asset class.
- Preserves the utility of the Bitcoin protocol by decoupling its technological value from the potential reputational damage of its creator.
❌ Cons
- Directly undermines the core principle of fungibility, potentially creating a ‘two-tier’ Bitcoin system that weakens the network effect.
- Relies on the ‘Patoshi pattern’ and other forensic heuristics which, while statistically strong, lack 100% cryptographic certainty.
- Could be perceived as a ‘soft-fork’ by financial proxy, leading to ideological fractures within the Bitcoin community.
- The creation of such a hedge might inadvertently signal a lack of confidence, triggering the very volatility it seeks to mitigate.
📊 Feasibility
Moderate. While the financial engineering required to create ‘Clean-Chain’ derivatives is well within the capabilities of modern Sovereign Wealth Funds, the primary hurdle is achieving international consensus on the specific UTXOs (Unspent Transaction Outputs) that constitute the ‘Satoshi stash’.
💥 Impact
This framework would likely lead to a bifurcated market where ‘Clean-Chain’ BTC trades at a significant premium. It would effectively neutralize the ‘$100B Silence Problem’ by pricing the potential dump into a separate, hedged instrument, thereby stabilizing the global economy against ‘Origin Risk’ shocks.
⚠️ Risks
- The ‘Satoshi Reveal’ could involve a benign or non-hostile entity, rendering the expensive hedging infrastructure a massive sunk cost.
- Hostile state actors could use the derivative market itself to execute ‘short-and-distort’ attacks on the ‘Clean-Chain’ valuation.
- Fragmentation of liquidity between ‘Clean’ and ‘Legacy’ Bitcoin could increase overall market slippage and volatility during crises.
- Regulatory capture, where governments use ‘Clean-Chain’ definitions to arbitrarily blacklist coins belonging to political dissidents.
📋 Requirements
- Standardized, high-confidence cryptographic forensics to identify and track the 1.1 million dormant ‘Satoshi’ coins.
- International legal frameworks defining ‘Origin-Risk’ and the status of ‘Clean-Chain’ financial products.
- Institutional-grade blockchain oracles to provide real-time data on the movement of dormant whale wallets to derivative smart contracts.
- Sovereign-level capital commitment to provide the necessary liquidity for a global ‘Origin-Risk’ insurance market.
Option 4 Analysis: Deep-Web Packet Reconstruction of the 2008-2009 P2P Network
✅ Pros
- Provides empirical, infrastructure-based evidence that bypasses the limitations of linguistic or stylistic analysis of Satoshi’s writings.
- Could potentially resolve the ‘$100B Silence Problem’ by identifying if the originating hardware was located in a seized facility or a defunct state laboratory.
- Establishes a new methodology for ‘Cyber-Archaeology’ that can be applied to other historical digital mysteries and early internet events.
- Offers a way to distinguish between a decentralized grassroots launch and a centralized state-sponsored ‘injection’ into the global network.
❌ Cons
- Extreme data scarcity: Most ISPs and backbone providers do not retain granular packet-level logs or netflow data for 15+ years.
- Obfuscation techniques: If Satoshi used Tor (available in 2008) or multi-hop proxies, the reconstructed ‘origin’ would only point to an exit node.
- Clock drift and timestamp inaccuracy: Early P2P logs often suffer from unsynchronized local clocks, making precise latency and hop-count triangulation unreliable.
- High probability of ‘dead ends’ where the trail terminates at a defunct ISP or a recycled IP block.
📊 Feasibility
Low to Moderate. While the signal processing algorithms are advanced enough, the primary bottleneck is the acquisition of ‘dark data’—archived logs from 2008-2009 that are likely only held by intelligence agencies or a few elite university network repositories.
💥 Impact
High. Definitive proof of a state-actor origin (like North Korea) could trigger massive geopolitical shifts, regulatory crackdowns, and a potential re-evaluation of Bitcoin’s status as a ‘neutral’ asset. Conversely, proof of a private residence origin would solidify the ‘immaculate conception’ narrative.
⚠️ Risks
- False Positives: Misinterpreting a relay node as the origin point could lead to the wrongful ‘doxing’ of an innocent early adopter or a specific geographic region.
- Market Destabilization: Any credible evidence linking the $100B in silent coins to a sanctioned state entity could cause a catastrophic liquidity event or a forced hard-fork.
- Cyber-Retaliation: Investigating state-controlled IP ranges from that era might trigger defensive or offensive responses from the state actors being scrutinized.
📋 Requirements
- Access to historical ‘NetFlow’ or PCAP data from Tier-1 providers and early internet exchange points (IXPs).
- Advanced signal processing expertise to filter noise from 2008-era global internet congestion.
- Collaboration with early ‘Cypherpunks’ who may have preserved personal node logs or debug files from the first 1,000 blocks.
- High-performance computing clusters to run simulations of the 2009 global network topology.
Option 5 Analysis: The ‘Satoshi Mythos’ as a Tool for Cognitive Warfare
✅ Pros
- Provides a sophisticated framework for understanding how the ‘$100B Silence’ functions as a psychological ‘Sword of Damocles’ over global markets.
- Exposes the tactical flexibility of state-controlled media in pivoting between ‘Bitcoin as Freedom’ (to encourage USD capital flight) and ‘Bitcoin as CIA/NSA Tool’ (to discourage domestic adoption).
- Offers intelligence agencies a predictive model for geopolitical shifts based on narrative changes in state-sponsored financial reporting.
- Reframes the mystery of Satoshi from a historical puzzle into an active, ongoing asset in information warfare.
❌ Cons
- The analysis is inherently speculative and risks falling into the same ‘conspiracy’ traps it seeks to document.
- Attributing intent to state-media narratives can be difficult, as they may simply be reflecting internal confusion rather than a coordinated cognitive strike.
- Focusing on the ‘State-Actor’ narrative may inadvertently lend it more credibility than it deserves, potentially damaging the decentralized ethos of the technology.
- Quantifying the actual impact of these narratives on the stability of the US Dollar is methodologically challenging.
📊 Feasibility
High for the research and documentation phase using Open Source Intelligence (OSINT) and sentiment analysis; however, counter-acting these narratives is difficult due to the decentralized and anonymous nature of the subject matter.
💥 Impact
Could fundamentally change how institutional investors and nation-states perceive ‘Satoshi’s stash,’ moving it from a financial risk to a geopolitical signaling device. It may also lead to increased regulatory scrutiny of crypto-narratives as a form of market manipulation.
⚠️ Risks
- The ‘Trojan Horse’ narrative could become a self-fulfilling prophecy, leading to aggressive state bans that stifle legitimate technological innovation.
- If a state actor successfully ‘claims’ the Satoshi identity (even falsely), it could trigger a massive liquidity crisis or a ‘run on the myth’ that devalues the asset.
- Analyzing cognitive warfare techniques may provide a blueprint for other actors to more effectively weaponize the $100B Silence Problem.
📋 Requirements
- Multi-lingual OSINT capabilities to monitor state-controlled media in Russia, China, Iran, and North Korea.
- Advanced sentiment analysis and natural language processing (NLP) tools to track narrative shifts over time.
- Expertise in ‘Reflexivity Theory’ and psychological operations (PSYOPs) within financial contexts.
- A comprehensive database of all historical movements (or lack thereof) in the Satoshi-era wallets to correlate with geopolitical events.
Option 6 Analysis: Honeypot Transaction Monitoring for ‘Satoshi-Era’ Wallet Activation
✅ Pros
- Provides an early warning system for unprecedented market volatility and potential ‘black swan’ events related to the $100B liquidity.
- Transforms passive observation into active intelligence gathering regarding state-actor liquidity and internal regime stability.
- Enables the capture of ephemeral network metadata (IP origins, node propagation patterns) that is lost if not monitored in real-time.
- Offers a definitive empirical test for the ‘State-Actor’ hypothesis; movement during specific geopolitical crises would provide high-confidence correlation.
- Allows for the identification of the specific software or hardware stack used to sign the transaction, potentially linking it to known state-sponsored cyber tools.
❌ Cons
- Highly susceptible to obfuscation techniques such as Tor, VPNs, or offline transaction signing (PSBTs) which mask the point of origin.
- Distinguishing between the actual owner and ‘dusting’ attacks (small amounts sent by third parties to the Satoshi addresses) is technically complex.
- The ‘$100B Silence’ might never break, rendering the entire surveillance infrastructure a permanent ‘sunk cost’ with no actionable output.
- Sophisticated actors could intentionally leak misleading metadata to frame a rival nation-state or individual.
- Ethical and legal gray areas regarding the mass surveillance of global network traffic to deanonymize specific blockchain users.
📊 Feasibility
Technically feasible but operationally complex. While monitoring the public ledger is trivial, capturing the underlying network-layer metadata requires a vast, globally distributed network of ‘sentry’ nodes and potential cooperation with Tier-1 internet service providers to be truly effective against a sophisticated state actor.
💥 Impact
A ‘thaw’ in these wallets would likely trigger an immediate and massive market correction. Beyond finance, it would force a global re-evaluation of Bitcoin’s ‘digital gold’ narrative, potentially shifting the asset’s perception toward that of a ‘geopolitical weapon’ or a state-controlled reserve.
⚠️ Risks
- False positives could trigger automated trading bots, causing flash crashes and unnecessary market panic.
- The actor may detect the surveillance and use it to ‘signal’ false intentions, manipulating global markets or diplomatic relations.
- Public discovery of such a high-level surveillance network could undermine global trust in the pseudonymity of the Bitcoin network, leading to a hard fork or mass migration to privacy coins.
- The system could be ‘blinded’ by a massive DDoS attack on the monitoring nodes precisely when the transaction occurs.
📋 Requirements
- A global array of high-performance Bitcoin nodes positioned at major internet exchange points (IXPs) to minimize latency.
- Advanced heuristic algorithms to filter out ‘dust’ and non-owner-initiated transactions in real-time.
- Deep-packet inspection (DPI) capabilities and timing analysis tools to correlate transaction broadcasts with physical geographic locations.
- A multi-disciplinary team of blockchain forensic analysts, network security experts, and geopolitical intelligence officers to interpret the ‘signal’.
Option 7 Analysis: The ‘Dark Satoshi’ Protocol for Sanction-Resistant State Finance
✅ Pros
- Provides absolute financial sovereignty for nations excluded from the SWIFT system and Western banking.
- Utilizes the ‘Silence Problem’ as a strategic asset, preventing adversaries from tracking or front-running state-level market moves.
- Protects national reserves from international asset freezes and seizures by making the ledger’s ownership layer invisible.
- Encourages a multi-polar financial world, reducing the impact of unilateral economic sanctions.
- Leverages advanced Zero-Knowledge proofs to allow for verifiable solvency without revealing specific transaction details or wallet balances.
❌ Cons
- Extreme difficulty in establishing liquidity; ‘silent’ reserves are hard to spend without creating an observable exit point.
- High barrier to entry for trade partners who may fear secondary sanctions for participating in an ‘invisible’ economy.
- The lack of transparency could facilitate internal corruption and embezzlement within the state leadership.
- Risk of protocol fragmentation if different sanctioned nations cannot agree on a unified consensus mechanism.
- Potential for massive market volatility if ‘silent’ reserves are suddenly moved or liquidated into the public economy.
📊 Feasibility
Technically high but geopolitically difficult. While the cryptographic tools (ZK-SNARKs, Ring Signatures, and Stealth Addresses) exist, the primary hurdle is the creation of a physical trade network (oil, minerals, food) that accepts these tokens as a medium of exchange outside the reach of traditional maritime and financial monitoring.
💥 Impact
The emergence of a ‘Shadow Global Economy’ that operates in parallel to the IMF/World Bank system. This would lead to the permanent erosion of the US Dollar’s role as a geopolitical tool and shift the focus of intelligence agencies from tracking bank transfers to breaking cryptographic protocols.
⚠️ Risks
- Total loss of national wealth if the underlying cryptographic keys are compromised or lost during a regime change.
- Aggressive cyber-warfare from dominant financial powers aimed at de-anonymizing the network or launching 51% attacks.
- The protocol could be used to hide hyper-inflation or the printing of ‘dark’ tokens, leading to a sudden collapse of the parallel economy.
- Accidental ‘permanent silence’ where funds become unrecoverable due to technical bugs in the obfuscation layer.
📋 Requirements
- A coalition of at least three resource-rich sanctioned nations to provide initial liquidity and utility.
- Development of ‘Obfuscated Mining’ hardware that can be hidden within existing industrial power grids to prevent heat-signature detection.
- Advanced ZK-Proof architecture capable of handling state-level transaction volumes with low latency.
- Secure, air-gapped hardware security modules (HSMs) for state-level key management.
- Integration with physical ‘dark’ shipping and logistics networks to facilitate the exchange of goods for tokens.
Option 8 Analysis: Silicon Fingerprinting of Early Mining Hardware Signatures
✅ Pros
- Provides an objective, data-driven forensic path that bypasses the limitations of linguistic or behavioral analysis.
- Utilizes the immutable nature of the blockchain, ensuring the source data hasn’t been tampered with since 2009.
- Can potentially link digital activity to physical supply chains and export control records, providing a ‘smoking gun’ for state-level involvement.
- Offers a way to explain the ‘$100B Silence’ by identifying if the hardware used was part of a decommissioned or classified government project.
❌ Cons
- The ‘Patoshi’ pattern (extra-nonce increments) is already known, but attributing it to specific silicon vs. custom software is highly speculative.
- Network latency and 2009-era clock drift introduce significant noise into timing-based analysis.
- Satoshi likely used standard C++ code which abstracts the hardware, potentially masking unique architectural signatures.
- Limited data points: 50,000 blocks provide a relatively small sample size for high-confidence hardware fingerprinting.
📊 Feasibility
Low to Moderate. While the blockchain data is public, the ‘ground truth’ (benchmarking 2009-era restricted FPGAs or specialized CPUs) requires access to rare hardware and sophisticated side-channel analysis expertise that is usually restricted to intelligence agencies.
💥 Impact
High. Definitive proof of state-actor hardware would collapse the ‘Cypherpunk’ origin narrative, potentially leading to massive market volatility and a geopolitical re-evaluation of Bitcoin as a strategic asset or weapon.
⚠️ Risks
- High risk of false positives where a clever software optimization is mistaken for a unique hardware signature.
- Geopolitical escalation if a specific nation-state is ‘proven’ to be the creator based on circumstantial hardware evidence.
- Potential to inadvertently deanonymize other early, non-Satoshi miners, compromising their safety.
📋 Requirements
- A library of 2009-era hardware (CPUs, early FPGAs, and ASICs) for comparative benchmarking.
- Deep expertise in SHA-256 hardware implementation and side-channel signal processing.
- Access to historical export control databases (e.g., Wassenaar Arrangement lists) from the 2008-2010 period.
- Advanced statistical models to filter out network-induced timing noise from hardware-induced processing signatures.
Brainstorming Results: Generate a broad, divergent set of ideas, extensions, and applications inspired by the Bitcoin Origin Probability Analysis (North Korea vs. Alternative Theories). Explore the geopolitical, technological, and narrative implications of the ‘State-Actor’ hypothesis versus individual creator theories.
🏆 Top Recommendation: The ‘Satoshi Mythos’ as a Tool for Cognitive Warfare
This initiative analyzes how the ambiguity of Bitcoin’s creator is weaponized by different regimes to undermine trust in the US Dollar. It documents how state-controlled media outlets alternate between the ‘Individual Genius’ and ‘State-Actor’ narratives to frame Bitcoin as either a tool for liberation or a Trojan horse, depending on their current diplomatic objectives.
Option 5 is the most strategically sound choice because it addresses the ‘narrative implications’ of the Satoshi mystery, which are currently active and exploitable, rather than focusing solely on the ‘identity’ which may remain permanently obscured. While forensic options (1, 4, and 8) face significant feasibility hurdles and high risks of false positives that could trigger geopolitical crises, Option 5 utilizes high-feasibility OSINT and sentiment analysis to provide immediate actionable intelligence. It allows policymakers to understand and neutralize how the ‘State-Actor’ hypothesis is being weaponized to undermine financial trust, making it a proactive defense against cognitive warfare. It is superior to Option 6 because it analyzes the ‘why’ and ‘how’ of the myth’s usage, rather than just waiting for a ‘thaw’ in the coins that may never occur.
Summary
The brainstorming session successfully mapped the Bitcoin origin mystery across four critical domains: forensic attribution, geopolitical deterrence, financial risk management, and narrative warfare. The findings highlight that the 1.1 million ‘Satoshi coins’ are viewed by state actors not just as wealth, but as a strategic ‘financial nuclear option’ or a tool for destabilizing the US-led financial order. A key trend identified is the shift from viewing Bitcoin as a purely decentralized technology to a potential instrument of statecraft, necessitating a move toward ‘Clean-Chain’ derivatives and sophisticated narrative monitoring to protect global market stability.
Session Complete
Total Time: 199.207s Options Generated: 8 Options Analyzed: 8 Completed: 2026-03-03 12:44:29
Game Theory Analysis
Started: 2026-03-03 12:41:14
Game Theory Analysis
Scenario: The Satoshi Anonymity Game: Analyzing the strategic incentives for maintaining silence versus claiming the $100 billion Satoshi fortune, contrasting the rational payoffs for an individual creator versus a state actor like North Korea. Players: Individual Creator (e.g., Szabo/Finney), State Actor (e.g., North Korea), Global Financial Regulators/Tax Authorities
Game Type: non-cooperative
Game Structure Analysis
This analysis explores the strategic interaction between a potential creator of Bitcoin and global authorities, focusing on the divergence in rational behavior between an individual and a state actor.
1. Identify the Game Structure
- Game Type: Non-cooperative, Dynamic (Sequential). The “Satoshi” entity moves first (by maintaining silence or revealing), and Regulators/Tax Authorities move second (by reacting to that revelation).
- Duration: Repeated Game. In every “round” (time period), the creator chooses whether to break silence. The game continues as long as the identity remains a secret.
- Information: Imperfect and Asymmetric. The creator has perfect information regarding their identity and private keys. The Regulators have imperfect information, attempting to deduce the identity through forensics.
- Asymmetries: There is a profound Utility Asymmetry. The value of $100 billion and the cost of “Aggressive Prosecution” are weighed differently by a single human (who has a finite lifespan and physical vulnerability) versus a state (which has institutional longevity and sovereign immunity).
2. Define Strategy Spaces
Player 1: The Creator (Individual or State Actor)
- Maintain Silence (OPSEC): Keep the “Patoshi” coins unmoved. Forego the use of the $100B fortune to preserve anonymity.
- Claim Credit / Reveal: Move the coins to an exchange or sign a message. This grants access to the fortune but triggers a regulatory response.
- Strategic Exploitation (State Actor Only): Use the underlying technology or market influence to bypass sanctions or conduct cyber-warfare without explicitly claiming the “Satoshi” title.
Player 2: Global Regulators / Tax Authorities
- Passive Monitoring: Observe blockchain movements without taking legal action unless a crime is proven.
- Aggressive Prosecution/Taxation: Upon revelation, immediately freeze assets, demand back-taxes (potentially exceeding 50%), and investigate the origin of the software for “Money Transmitter” violations.
3. Characterize Payoffs
The payoffs are non-transferable and depend heavily on the nature of the Creator.
The Individual Creator (IC) Payoff Matrix
For an individual, the utility of $100B is subject to diminishing marginal utility, while the “disutility” of life imprisonment or total loss of privacy is infinite.
| Strategy Pair | IC Payoff | Regulator Payoff |
|---|---|---|
| Silence / Passive | $0 (Financial), High (Security) | Low (Uncollected Tax) |
| Reveal / Passive | High (Wealth + Prestige) | Medium (Tax Revenue) |
| Reveal / Aggressive | Negative (Legal Ruin/Security Risk) | High (Political Win/Revenue) |
- The Silence Paradox: For a rational individual, “Silence” is usually a dominated strategy because the opportunity cost ($100B) is so high. However, if the “Aggressive Prosecution” payoff is sufficiently negative (e.g., death or life in prison), “Silence” becomes a defensive equilibrium.
The State Actor (SA - North Korea) Payoff Matrix
For a state, the $100B is a “strategic reserve,” but the existence of the Bitcoin ecosystem itself is a tool for Asymmetric Warfare.
| Strategy Pair | SA Payoff | Regulator Payoff |
|---|---|---|
| Silence / Passive | Very High (Sanctions Evasion Tool) | Low (Systemic Risk) |
| Reveal / Aggressive | Low (Coins Blacklisted, Tool Destroyed) | High (Sanctions Enforcement) |
- Strategic Utility: For North Korea, the utility of Bitcoin as a “Sanctions Evasion Engine” outweighs the utility of cashing out the $100B. If they reveal, the coins are blacklisted and the “immaculate conception” myth of Bitcoin is destroyed, potentially devaluing the very tool they use to bypass the USD.
4. Key Features & Analysis
The Hundred Billion Silence Paradox
The source text highlights a central paradox: Why has the world’s largest fortune remained untouched?
- Individual Rationality: A human creator (Szabo/Finney) would eventually face a “liquidity requirement” or a desire for legacy. To stay silent for 15 years while holding $100B suggests the player is either deceased or the risks (legal/physical) are perceived as 100% fatal.
- State Rationality: For a state actor like North Korea, “Silence” is the dominant strategy. The $100B serves as a “Nuclear Option” for the economy. Moving it would alert every intelligence agency in the world, leading to the immediate “hard-forking” or blacklisting of those specific UTXOs.
Signaling and Commitment
- Satoshi’s Silence as a Signal: The continued silence signals to the market that Bitcoin is “decentralized” and “leaderless.” This signal increases the total market cap, which benefits a state actor using the network for smaller, stealthy thefts (Strategic Exploitation).
- Information Asymmetry: The Creator knows the “True Cost” of revelation. If the Creator is a state actor, the cost of revelation includes the loss of a multi-billion dollar annual revenue stream from cyber-theft (which relies on the legitimacy of the crypto-ecosystem).
Equilibrium Analysis
- Nash Equilibrium: In the current state, the game is in a Pooling Equilibrium. Both the “Individual” and the “State Actor” are currently choosing “Silence,” but for different reasons.
- The Shift: If Regulators signal a “Tax Amnesty” or “Legal Immunity” (changing the IC’s payoff for ‘Reveal’ from negative to positive), and the Creator still remains silent, the probability shifts heavily toward the State Actor hypothesis. A state actor is immune to individual incentives like “amnesty” because their goals are geopolitical, not personal.
Conclusion
The game theory analysis suggests that while “Silence” is a high-cost, defensive move for an Individual, it is a high-utility, offensive move for a State Actor. The “Hundred Billion Silence Paradox” is best resolved by identifying the player for whom the existence of the system is more valuable than the liquidation of the assets. For North Korea, Bitcoin is a weapon; for an individual, it is a fortune. Weapons are most effective when the enemy cannot pinpoint the trigger.
Payoff Matrix
This analysis evaluates the strategic interaction between the potential creators of Bitcoin and global authorities. The core of this game is the “Hundred Billion Silence Paradox”: the observation that for an individual, “Silence” is a dominated strategy (yielding near-zero utility compared to massive wealth), whereas for a state actor, “Silence” is the dominant strategy (preserving a vital tool for asymmetric warfare).
1. Game Structure Overview
- Type: Non-cooperative, asymmetric information game.
- Players: Individual Creator (IC), State Actor (NK), and Global Regulators (GR).
- Information: Imperfect (Regulators do not know the identity; IC/NK know their own identity but not the Regulators’ future level of aggression).
- Asymmetry: The IC seeks personal utility (wealth/safety), while the NK seeks institutional utility (sanctions evasion/geopolitical power).
2. Payoff Matrix: Individual Creator (IC) vs. Global Regulators (GR)
This matrix explores why “Silence” is considered a paradox for a rational individual.
| IC Strategy \ GR Strategy | Aggressive Prosecution/Taxation | Passive Monitoring |
|---|---|---|
| Claim Credit | IC: 5 / GR: 8 Outcome: IC gains ~$50B (after 50% tax/legal fees) and global fame, but faces lifelong surveillance and legal risk. GR gains massive tax revenue and a “win.” |
IC: 10 / GR: 2 Outcome: IC gains ~$100B and prestige with minimal interference. GR loses control over the narrative and potential revenue. |
| Maintain Silence | IC: 1 / GR: 0 Outcome: IC has $0 liquidity and no prestige. GR spends resources hunting a ghost. |
IC: 1 / GR: 1 Outcome: Status quo. IC remains anonymous but effectively “poor” relative to their potential. GR monitors the ledger. |
Analysis of the Individual Paradox:
- Dominated Strategy: For a living individual, Silence is technically a dominated strategy. Even in the worst-case “Aggressive Prosecution” scenario, a payoff of 5 (becoming a multi-billionaire under house arrest) is arguably superior to a payoff of 1 (living a normal life while $100B sits idle).
- The “Finney” Exception: If the IC is deceased (e.g., Hal Finney), the payoff for “Claim” drops to 0 for the individual, making Silence the only remaining state.
3. Payoff Matrix: State Actor (NK) vs. Global Regulators (GR)
This matrix illustrates why a state actor values OPSEC (Silence) above all else.
| NK Strategy \ GR Strategy | Aggressive Prosecution/Taxation | Passive Monitoring |
|---|---|---|
| Maintain OPSEC (Silence) | NK: 9 / GR: 4 Outcome: NK continues using BTC for sanctions evasion and money laundering. GR attempts to block on-ramps but fails to stop the protocol. |
NK: 10 / GR: 1 Outcome: NK exploits the system with maximum efficiency. GR remains oblivious to the state-level threat. |
| State Revelation | NK: 2 / GR: 9 Outcome: NK gains “geopolitical signaling” points, but the West likely “hard-forks” or blacklists the Satoshi coins, destroying the tool’s value. GR wins by neutralizing the threat. |
NK: 4 / GR: 5 Outcome: NK proves its technical prowess. GR is forced to react, eventually leading to the tool’s degradation. |
Analysis of the State Strategy:
- Dominant Strategy: Maintain OPSEC is the dominant strategy for a state actor. The utility of Bitcoin as a “Sanctions Evasion Engine” (worth billions in ongoing cash flow) far outweighs the one-time prestige of claiming its creation.
- Asymmetric Warfare: For NK, the $100B in the Satoshi wallet is not “money to be spent” but a deterrent or a dormant reserve. Moving it would reveal the origin and invite a coordinated global strike against the Bitcoin network’s legitimacy.
4. Summary of Payoffs and Strategic Equilibrium
Numerical Ranking Scale:
- 10: Maximum Utility (Total Wealth / Strategic Dominance)
- 5: Moderate Utility (Wealth with high costs / Partial Signaling)
- 0-1: Minimum Utility (Status Quo / Loss of Asset)
| Strategy Combination | Individual Creator (IC) Payoff | State Actor (NK) Payoff | Rationale |
|---|---|---|---|
| Silence + Passive Regulators | 1 | 10 | The Paradox: Low utility for an individual (wasted wealth), but maximum utility for a state (perfect tool). |
| Claim/Reveal + Passive Regulators | 10 | 4 | High utility for an individual (prestige/wealth), but low for a state (burns the asset). |
| Silence + Aggressive Regulators | 1 | 9 | Individual remains “poor”; State continues asymmetric warfare despite friction. |
5. Key Findings: The “Hundred Billion Silence Paradox”
- Individual Irrationality: In a standard rational choice model, an individual creator (like Szabo) remaining silent while being alive and capable of claiming $100B is an anomaly. The “costs” of fame/taxation rarely exceed the utility of $100B.
- State Rationality: For North Korea, the $100B is a “Sunk Cost” of creating the system. Their real payoff comes from the systemic utility of Bitcoin (laundering stolen funds, bypassing SWIFT). Revelation would lead to a “Kill Switch” event (regulatory blacklisting), making Silence the only rational move.
- Nash Equilibrium: The current state of the game is a Nash Equilibrium where the Creator (likely a State or a deceased Individual) maintains Silence and Regulators maintain Passive Monitoring/Archaeology. Neither party gains by unilaterally changing their strategy without more information.
Nash Equilibria Analysis
Based on the strategic incentives described in the “Hundred Billion Silence Paradox” and the provided analysis of Bitcoin’s origins, the following Nash Equilibria emerge. This analysis assumes a non-cooperative environment with asymmetric payoffs between individual and state actors.
Equilibrium 1: The State-Actor OPSEC Equilibrium
1. Strategy Profile:
- State Actor (NK): Maintain OPSEC (Silence).
- Global Regulators: Passive Monitoring / Ineffective Enforcement.
2. Why it is a Nash Equilibrium:
- State Actor: If North Korea reveals itself as Satoshi, the $100 billion fortune would be immediately blacklisted by global exchanges, and the “tool” (Bitcoin) would lose its utility for sanctions evasion. By staying silent, they retain the ability to use the network for asymmetric warfare and gradual exploitation. They cannot improve their payoff by deviating to “Reveal” because revelation destroys the asset’s liquidity and invites geopolitical retaliation.
- Regulators: Without a clear target or “smoking gun,” regulators cannot move to “Aggressive Prosecution.” Their best response to perfect OPSEC is passive monitoring to save enforcement costs.
3. Classification:
- Pure Strategy Equilibrium. The payoffs for a state actor are heavily weighted toward the long-term systemic utility of the network rather than the immediate prestige of the creator.
4. Stability and Likelihood:
- High Stability: This is the most stable equilibrium. It explains the 14+ years of silence. For a state, the “prestige” of creation is a negative utility (it invites scrutiny), making silence the strictly dominant strategy.
Equilibrium 2: The Individual-Actor “Rational Claim” Equilibrium
1. Strategy Profile:
- Individual Creator: Claim Credit (Access Fortune).
- Global Regulators: Aggressive Prosecution / Taxation.
2. Why it is a Nash Equilibrium:
- Individual Creator: For a living individual, “Silence” is a dominated strategy. Even with a 90% tax rate and legal fees, 10% of $100 billion ($10 billion) provides infinitely more utility than $0. An individual cannot improve their payoff by moving back to “Silence” once the opportunity cost of the fortune exceeds their fear of the state.
- Regulators: Once an individual identifies themselves, the regulator’s best response is to tax and prosecute to assert authority and collect revenue. They cannot improve their payoff by remaining passive once a taxable entity is identified.
3. Classification:
- Pure Strategy Equilibrium. This is the “Rational Exit” scenario.
4. Stability and Likelihood:
- Low Stability (The Paradox): This equilibrium is logically sound but empirically absent. The fact that no individual has moved to this equilibrium suggests either:
- The individual is dead (Hal Finney).
- The individual is not a rational economic actor.
- The “Individual Theory” is incorrect, and we are actually in Equilibrium 1.
Equilibrium 3: The “Dead Creator” Stasis (Pseudo-Equilibrium)
1. Strategy Profile:
- Individual Creator: Forced Silence (Incapacitated/Dead).
- Global Regulators: Passive Monitoring.
2. Why it is a Nash Equilibrium:
- This is a technical Nash Equilibrium because the “Player” (Individual) has no available moves. If the keys are lost or the creator is deceased, the strategy “Silence” becomes the only possible state. Regulators, seeing no movement in the “Patoshi” wallets, remain in a state of passive monitoring.
3. Classification:
- Pure Strategy Equilibrium (by constraint).
Comparison and Coordination Analysis
1. Which is most likely to occur?
The State-Actor OPSEC Equilibrium (Equilibrium 1) is the most likely to be currently active. The “Hundred Billion Silence Paradox” posits that for any rational human, the utility of $100B outweighs the utility of privacy. Since the money has not moved, the actor must be one for whom the existence of the system is more valuable than the liquidation of the coins. A state actor (like NK) fits this profile perfectly, as they use the system to bypass the very regulators who would seize the coins upon revelation.
2. Coordination Problems
There is a significant Information Asymmetry coordination problem. If the creator is a team (Theory 4), they face a “Prisoner’s Dilemma.” Any single member could defect and claim the $100B, ruining the silence for the others. The fact that no one has defected in 14 years strongly suggests either a single entity with absolute discipline (a State) or a player who is no longer capable of moving.
3. Pareto Dominance
- Equilibrium 1 (State Silence) is Pareto Dominant for the State Actor, as it preserves the geopolitical utility of Bitcoin.
- Equilibrium 2 (Individual Claim) would be Pareto Dominant for Regulators, as it results in massive tax revenue and legal closure.
- The conflict between these two equilibria defines the current “Cold War” of Bitcoin forensics. The State Actor’s “Silence” strategy successfully prevents the Regulators from reaching their preferred “Aggressive” payoff.
Summary Table: Nash Equilibrium Comparison
| Equilibrium | Actor Strategy | Regulator Strategy | Stability | Rationality Basis |
|---|---|---|---|---|
| State OPSEC | Silence | Passive | Very High | Strategic utility > Liquid wealth |
| Individual Claim | Claim | Aggressive | Moderate | Liquid wealth > Privacy |
| Dead Creator | Silence | Passive | Absolute | No moves available |
Conclusion: The “Silence” observed in the blockchain is a dominated strategy for a rational individual but an optimal Nash strategy for a state actor. This asymmetry is the strongest game-theoretic evidence for the North Korean (or state-level) origin theory.
Dominant Strategies Analysis
This analysis evaluates the strategic choices within the Satoshi Anonymity Game, focusing on the “Hundred Billion Silence Paradox.” We examine why the strategy of “Silence” functions differently for an individual versus a state actor.
1. Strictly Dominant Strategies
Definition: A strategy that provides a higher payoff than any other strategy, regardless of the competitors’ actions.
- State Actor (North Korea): Maintain OPSEC (Silence)
- Reasoning: For a state actor under heavy international sanctions, the utility of Bitcoin is not found in “cashing out” for prestige, but in its function as a tool for asymmetric warfare and sanctions evasion.
- If NK reveals itself, the $100 billion fortune (the “Patoshi” coins) would be immediately blacklisted by Global Regulators, rendered illiquid, and potentially seized.
- By maintaining silence, the state preserves the “Moneyness” of the asset and the integrity of the network as a shadow financial system. Therefore, Silence is strictly dominant because the geopolitical utility of an untraceable financial weapon exceeds the utility of a frozen $100 billion trophy.
2. Weakly Dominant Strategies
Definition: A strategy that is at least as good as any other strategy in all scenarios and better in at least one.
- Global Regulators: Passive Monitoring
- Reasoning: As long as the Satoshi coins remain stationary, the cost of “Aggressive Prosecution” is high with zero tax/legal yield. Passive monitoring allows regulators to conserve resources while waiting for a “Signaling” event (a wallet move). It is weakly dominant because it avoids the high political and legal costs of chasing a ghost, while remaining positioned to act if the status quo changes.
3. Dominated Strategies
Definition: A strategy that is always worse than at least one other available strategy.
- Individual Creator: Maintain Silence (The Paradox)
- Reasoning: For a rational, living individual (e.g., Szabo), “Silence” is a strictly dominated strategy.
- The Payoff Gap: The utility of “Claiming Credit” includes access to $100 billion, global historical prestige, and the ability to fund any security or legal defense required. Even with a 50% tax rate and $1 billion in security costs, the net utility of ~$49 billion + prestige is infinitely higher than the $0 utility of remaining silent while living in relative obscurity.
- Strategic Implication: The fact that the individual has not claimed the fortune suggests they are either irrational, dead (e.g., Hal Finney, where the strategy space is removed), or not the player (supporting the State Actor theory).
- State Actor: State Revelation
- Reasoning: This is a strictly dominated strategy. Revealing state authorship would trigger a “hard fork” or a global consensus to invalidate those specific coins. It would destroy the very tool the state spent years cultivating. There is no scenario where the “prestige” of creating Bitcoin outweighs the loss of a multi-billion dollar sanctions-evasion engine.
4. Iteratively Eliminated Strategies
Definition: Strategies removed from consideration because a rational player would never choose them, leading to a refined equilibrium.
- Eliminate “State Revelation”: Since this is dominated for the State Actor, Regulators can assume that if a revelation occurs, it is likely an Individual Creator or a sophisticated hoax.
- Eliminate “Individual Silence”: Since silence is dominated for a rational living individual, Regulators and Analysts can eliminate the “Living Individual Creator” from the probability pool of a silent Satoshi.
- Resulting Equilibrium: The game reaches a Nash Equilibrium at (State Actor: Maintain OPSEC) / (Regulators: Passive Monitoring).
Strategic Implications: The “Silence Paradox”
| Feature | Individual Creator (Rational) | State Actor (NK) |
|---|---|---|
| Primary Goal | Wealth Maximization / Prestige | Regime Survival / Sanctions Evasion |
| Utility of $100B | High (Life-changing) | Low (If coins are blacklisted/frozen) |
| Cost of Silence | Opportunity cost of $100B | Zero (Silence is the shield) |
| Strategic Conclusion | Silence is Irrational | Silence is Optimal |
1. The Death of the Individual Theory
The game theory suggests that the “Individual Creator” theory only holds if the player is no longer a “rational actor” (i.e., they are deceased). If the creator is alive, the continued silence is a strategic anomaly that contradicts standard economic utility models.
2. Asymmetric Utility
The game highlights an asymmetry of utility. For an individual, the money is the prize. For a state actor like North Korea, the anonymity of the system itself is the prize. This makes the State Actor the only player for whom “Silence” is a winning move in the long term.
3. Regulatory Stasis
Global Regulators are stuck in a “Wait and See” strategy. Because they cannot prosecute a pseudonym without a physical entity, and the State Actor has no incentive to provide one, the game remains in a perpetual state of Strategic Silence. This silence is not a vacuum of action, but a deliberate, dominant choice by a state-level entity to preserve a vital geopolitical tool.
Pareto Optimality Analysis
This analysis evaluates the Pareto optimal outcomes of the Satoshi Anonymity Game, focusing on the divergence between an Individual Creator and a State Actor (North Korea) under the pressure of the “Hundred Billion Silence Paradox.”
1. Identification of Pareto Optimal Outcomes
In this game, an outcome is Pareto optimal if no player can improve their utility without reducing the utility of another. Based on the strategic incentives, we identify two primary Pareto optimal frontiers depending on the identity of “Satoshi.”
Outcome A: The “Status Quo” (Silence, Silence, Passive)
- Strategies: [Individual/State: Silence] + [Regulators: Passive Monitoring]
- Utility:
- Individual: Low (Wealth is inaccessible; “Silence Paradox” suggests this is sub-optimal).
- State (NK): High (Preserves the “asymmetric weapon,” avoids immediate sanctions on the 1M BTC, maintains plausible deniability).
- Regulators: Medium (Market stability is preserved; no costly “witch hunts”).
- Pareto Status: Optimal for the State Actor scenario. Any move by NK to “Reveal” makes them worse off (sanctions/blacklisting), and any move by Regulators to “Aggressive” costs resources without guaranteed recovery.
Outcome B: The “Great Settlement” (Claim, Passive/Negotiated)
- Strategies: [Individual: Claim Credit] + [Regulators: Passive/Negotiated Taxation]
- Utility:
- Individual: Maximum (Access to $100B, prestige, legal certainty).
- Regulators: High (Massive tax windfall, regulatory clarity, end of uncertainty).
- Pareto Status: Optimal for the Individual Creator scenario. This is the “rational” end-state for a human actor. To move away from this (e.g., back to Silence) makes both the Individual and the Tax Authority worse off.
2. Comparison: Pareto Optimal Outcomes vs. Nash Equilibria
| Feature | Nash Equilibrium (Individual) | Nash Equilibrium (State Actor) | Pareto Optimal (Ideal) |
|---|---|---|---|
| Outcome | (Claim, Aggressive) | (Silence, Aggressive) | (Claim, Passive/Negotiated) |
| Description | Individual claims; Regulators prosecute/tax heavily. | NK stays silent; Regulators hunt aggressively. | Individual claims; Regulators provide a “safe harbor” for tax. |
| Stability | Stable; neither can change without loss. | Stable; NK won’t reveal, Regulators won’t stop. | Unstable; Regulators tempted to “defect” to Aggressive. |
- The Individual’s Nash Trap: For an individual, the Nash Equilibrium is often (Claim, Aggressive). Even if the individual knows they will be taxed 90%, $10B is better than $0 (Silence). However, this is Pareto inefficient because both could be better off with a lower-friction, negotiated settlement (Passive/Negotiated).
- The State’s Nash Alignment: For North Korea, the Nash Equilibrium (Silence, Aggressive) is closer to a Pareto optimum for the state itself. Because the state values the existence of the tool for sanctions evasion more than the liquidity of the cash, Silence is a dominant strategy that Regulators cannot easily break.
3. Pareto Improvements over Equilibrium Outcomes
A Pareto improvement occurs when a change in strategy makes at least one player better off without making any player worse off.
- From (Claim, Aggressive) to (Claim, Passive/Negotiated):
- If Regulators offer a “Satoshi Amnesty” (Passive/Negotiated), the Individual gains utility (less legal stress/more wealth) and the Regulator gains utility (guaranteed revenue vs. protracted litigation). This is a clear Pareto improvement over the aggressive prosecution equilibrium.
- The “Silence” Deadlock: For an individual, moving from Silence to Claim is a Pareto improvement (they gain wealth, regulators gain tax). The fact that this hasn’t happened is the core of the Hundred Billion Silence Paradox, suggesting the “Individual” is either dead or the “State Actor” theory (where Silence is already optimal) is correct.
4. Efficiency vs. Equilibrium Trade-offs
The game highlights a massive gap between Strategic Equilibrium and Social/Economic Efficiency:
- The Cost of Anonymity: The current equilibrium of (Silence, Aggressive Monitoring) is highly inefficient. $100 billion in capital sits dormant (deadweight loss), and global regulators spend millions in surveillance.
- Information Asymmetry: The “State Actor” (NK) benefits from this inefficiency. Their utility is derived from the lack of transparency. In this case, the Nash Equilibrium (Silence) is efficient for the State’s goals of asymmetric warfare but inefficient for the global financial system.
- The Individual’s Risk Premium: For an individual like Szabo or Finney, the trade-off is between Wealth and Liberty. If the “Aggressive Prosecution” payoff includes life imprisonment (e.g., for launching an unlicensed MSB), then Silence—while economically inefficient—becomes a “Personal Nash Equilibrium.”
Conclusion: Opportunities for Coordination
To reach a Pareto-superior outcome (The Great Settlement), a commitment mechanism is required. If Global Regulators could credibly commit to a “Non-Prosecution Agreement” in exchange for a fixed tax percentage, the “Individual Creator” would have a rational path to exit Silence.
The absence of such a move suggests one of two things:
- The State Actor Hypothesis: The player is North Korea, for whom “Silence” is not a paradox but a high-utility strategic choice for sanctions evasion.
- The Credible Threat: The Individual believes Regulators cannot resist the “Aggressive” strategy once the identity is revealed, making the Pareto-optimal “Settlement” impossible to achieve.
Strategic Recommendations
Based on the game theory analysis of the Satoshi Anonymity Game and the Hundred Billion Silence Paradox, the following strategic recommendations are provided for each player.
1. Individual Creator (e.g., Szabo, Finney, or a Private Team)
- Optimal Strategy: Maintain Silence (The “Shield of Anonymity”). Despite the $100 billion opportunity cost, the rational individual should prioritize security. The utility of $100B is marginally lower than the disutility of state-level pursuit, kidnapping risk, and 90%+ effective taxation/legal seizure.
- Contingent Strategies:
- If Regulators offer Amnesty: If a major jurisdiction (e.g., USA) offers a “Satoshi Law” (guaranteed immunity and capped tax), move toward a Partial Revelation to secure a fraction of the wealth.
- If Doxxed by Third Party: Immediately execute a “Burn Strategy” (cryptographically proving the coins will never move) to remove the incentive for criminals to kidnap/torture the creator.
- Risk Assessment: The primary risk is “Protocol Obsolescence.” If the Bitcoin network forks or evolves to invalidate the original coins, the “Silence” strategy results in a total loss of the $100B asset.
- Coordination Opportunities: Minimal. Any attempt to coordinate with others increases the “Leak Probability” exponentially.
- Information Considerations: Use a Dead Man’s Switch. Ensure that information is released only posthumously to provide for heirs while protecting the living creator.
2. State Actor (e.g., North Korea)
- Optimal Strategy: Strategic Exploitation & Permanent OPSEC. For a state, the Satoshi coins are a “Nuclear Option” that is more valuable as a deterrent or a shadow tool than as realized cash. Claiming the fortune would likely trigger a global hard-fork to blacklist those coins, rendering them worthless.
- Contingent Strategies:
- If Sanctions Become Existential: Use the threat of moving the coins to crash the market as Geopolitical Signaling (Financial Mutually Assured Destruction).
- If Attribution is Leaked: Pivot to State Revelation and claim the creation as a triumph of national ideology (e.g., Juche) to gain soft power in the Global South.
- Risk Assessment: The “Attribution Risk.” If Western intelligence proves state origin, the entire Bitcoin network could be labeled a “Sanctions Evasion Tool,” leading to institutional divestment and a price collapse.
- Coordination Opportunities: Coordinate with other “Pariah States” to create a Bitcoin-based trade bloc that bypasses the SWIFT system, using the Satoshi prestige as a foundational myth.
- Information Considerations: Maintain “Strategic Ambiguity.” Neither confirm nor deny, allowing the myth to facilitate the adoption of the tool.
3. Global Financial Regulators / Tax Authorities
- Optimal Strategy: Passive Monitoring & Off-Ramp Control. The cost of “hunting” Satoshi is high with low probability of success. The optimal move is to “Wait at the Exit.” Ensure all major exchanges have “Satoshi Alerts” to freeze any movement immediately.
- Contingent Strategies:
- If an Individual Emerges: Offer a Settlement Path. It is better to collect 40% tax on $100B ($40B) via a deal than 0% via a protracted legal battle that drives the creator underground.
- If a State Actor Emerges: Initiate Protocol-Level Sanctions. Work with miners and developers to “soft-fork” the Satoshi UTXOs into a frozen state.
- Risk Assessment: “Regulatory Overreach.” If regulators are too aggressive, they may inadvertently trigger a “Privacy War” where the community develops even more untraceable technologies.
- Coordination Opportunities: Use the FATF (Financial Action Task Force) to ensure that no single “Tax Haven” can provide a safe harbor for the Satoshi fortune.
- Information Considerations: Signal “Forensic Omniscience.” Publicly demonstrate advanced blockchain analysis capabilities to discourage the creator from attempting to move funds.
Overall Strategic Insights
- The Asymmetry of Silence: Silence is a cost for the individual (lost wealth) but a benefit for the state (preserved strategic tool). This explains why the “Satoshi” entity acts more like a state than a person.
- The Fork Deterrent: The threat of a community-led “Hard Fork” acts as a check on the creator. If Satoshi moves the coins in a way the market dislikes, the market can simply “delete” Satoshi’s coins via a code update.
- The Prestige Trap: For individuals, “Prestige” is a trap that leads to “Taxation and Prosecution.” For states, “Prestige” is a geopolitical asset.
Potential Pitfalls to Avoid
- For the Individual: Avoid “Small Movements.” Moving even 0.1 BTC from a Satoshi-linked wallet provides enough forensic data to potentially deanonymize the entire stack.
- For the State: Avoid “Market Crashing.” If the state actor sells too much too fast, they destroy the very liquidity they need for long-term sanctions evasion.
- For Regulators: Avoid “Demonizing the Protocol.” Attacking Bitcoin itself because of its creator’s identity risks alienating the broader financial sector now integrated with the asset.
Implementation Guidance
- Execution of Silence: The creator should utilize “Air-Gapped” legacy systems. Any digital interaction with the Satoshi keys in the modern internet environment (post-2020) is significantly more dangerous than it was in 2011 due to advanced heuristic clustering.
- Monitoring the “Patoshi” Pattern: Regulators should focus on the “Patoshi” blocks (the first ~1M BTC). These are the only moves that matter for the “Hundred Billion Silence Paradox.”
- State-Level Integration: If a state actor is the creator, they should focus on “Mining Dominance” rather than “Wallet Movement” to laundered their influence into the network.
Game Theory Analysis Summary
GameAnalysis(game_type=Signaling Game with Incomplete Information (Asymmetric Information), players=[The Creator (Satoshi), The Global System (Regulators/Market)], strategies={The Creator (Satoshi)=[Reveal/Claim, Maintain Silence], The Global System (Regulators/Market)=[Co-opt/Integrate, Attack/Sanction]}, payoff_matrix=Individual Creator: Reveal (High Wealth + Fame - Legal/Safety Risk) vs Silence ($0 Liquid + Safety). State Actor: Reveal (Asset Seizure + Diplomatic Crisis) vs Silence (Sanctions Evasion + Strategic Option Value). Market: Integration (Legitimate Asset Class) vs Attack (Freeze Assets)., nash_equilibria=[The ‘Silence Equilibrium’: The Creator chooses Silence and the Market chooses Integration.], dominant_strategies={North Korea (State Actor)=Silence, The Market=Integration}, pareto_optimal_outcomes=[The Status Quo: The current state (Creator Silence + Market Growth)], recommendations={Regulators/Intelligence=Shift focus from ‘Who is Satoshi?’ to ‘What entity benefits most from the Silence Equilibrium?’, Investors=Monitor the ‘Patoshi’ wallets as the primary signal of a ‘Game State Change.’, Forensic Researchers=Prioritize ‘Blockchain Archaeology’ to identify if the original mining patterns suggest institutional/team-level coordination.})
Analysis completed in 121s Finished: 2026-03-03 12:43:16
Multi-Perspective Analysis Transcript
Subject: Bitcoin Origin Probability Analysis: North Korea vs Alternative Theories
Perspectives: National Security & Intelligence, Cryptocurrency Community & Cypherpunks, Financial Regulators & Institutional Investors, Academic & Technical Researchers
Consensus Threshold: 0.7
National Security & Intelligence Perspective
This analysis examines the “Bitcoin Origin Probability Analysis” through the lens of National Security and Intelligence (NS&I). From this perspective, the identity of Satoshi Nakamoto is not merely a historical curiosity but a matter of strategic attribution, financial stability, and asymmetric warfare capability.
1. Strategic Intelligence Analysis: The DPRK Hypothesis
From an NS&I viewpoint, the theory that North Korea (DPRK) created Bitcoin is a high-impact, medium-probability hypothesis that aligns with the “Juche” doctrine of self-reliance and the Reconnaissance General Bureau’s (RGB) mandate for illicit revenue generation.
- The “Long Game” Doctrine: Intelligence agencies prioritize intent and persistence. The DPRK is one of the few global actors with the institutional discipline to maintain a “14-year silence” regarding a $100B asset. For an individual, the “Silence Paradox” is a psychological anomaly; for a state intelligence service, it is a standard Operational Security (OPSEC) requirement to protect a strategic capability.
- The 2009 Currency Crisis Linkage: The timing of Bitcoin’s launch (January 2009) closely mirrors the DPRK’s disastrous 2009 currency revaluation, which wiped out domestic savings and heightened the regime’s desperation for non-sovereign, hard-currency alternatives.
- Asymmetric Financial Warfare: Bitcoin represents a “perfect” asymmetric tool. It undermines the efficacy of the U.S. Dollar-denominated sanctions regime (OFAC) and provides a censorship-resistant rail for Proliferation Financing (PF).
2. Key Considerations & Risks
A. The “Nuclear Option” in Finance
If the DPRK (or any hostile state) controls the “Satoshi wallets” (approx. 1.1 million BTC), they possess a financial weapon of mass disruption.
- Risk: A sudden liquidation of these assets could crash the crypto-economy, impacting Western institutional balance sheets and causing systemic volatility.
- Intelligence Gap: We currently lack “tripwire” intelligence that can definitively link the private keys of the genesis blocks to RGB-controlled infrastructure.
B. Technical Capability vs. “Cut-outs”
The analysis notes a “Capability Gap” in 2009. From an intelligence perspective, this gap could be bridged via clandestine procurement of talent.
- Risk: The DPRK may not have written the code but could have commissioned it through “cut-outs” (front companies) or coerced foreign experts, a common tactic in their nuclear and missile programs.
- Insight: The “Western Team” theory and “DPRK” theory are not mutually exclusive. A state actor could have co-opted a small group of cypherpunks.
C. Attribution Bias
The intelligence community must guard against confirmation bias. Because the DPRK is currently the most prolific crypto-thief (Lazarus Group), there is a tendency to retroactively attribute the origin to them.
- Risk: Over-focusing on the DPRK might lead to ignoring a “Black Swan” creator (e.g., a different state actor or a non-state militant group) using the protocol for similar anti-hegemonic purposes.
3. Opportunities for Intelligence Operations
- Blockchain Archaeology as SIGINT: Advanced forensic analysis of the “Patoshi” pattern (mining behavior) should be cross-referenced with known DPRK internet traffic patterns from 2009 (satellite links, Chinese IP backbones).
- Defector Debriefing: Prioritizing the debriefing of high-level defectors from Bureau 121 or the RGB specifically regarding early-stage research into distributed ledgers.
- Financial Intelligence (FININT): Monitoring the “Satoshi” coins is the ultimate “dead man’s switch.” Any movement in these wallets should be treated as a high-priority national security event, potentially signaling a shift in a state actor’s strategic posture.
4. Recommendations
- Formal Attribution Review: The Intelligence Community (IC) should conduct a formal National Intelligence Estimate (NIE) on the origins of Bitcoin, moving beyond “circumstantial alignment” to “technical forensics.”
- Sanctions Evolution: If the probability of state-origin increases, the Treasury Department must evolve sanctions from “address-blacklisting” to “protocol-level” risk assessments.
- Counter-Influence Operations: If a state actor is identified, the “legend” of Satoshi as a libertarian hero must be countered to prevent the asset from being used as a tool for ideological subversion against Western financial institutions.
5. Confidence Rating
Analysis Confidence Score: 0.85
- Rationale: The Bayesian framework provided is robust, and the “Strategic Alignment” arguments are highly consistent with observed state-actor behavior. However, the “Technical Capability Gap” remains the primary “known unknown” that prevents a higher confidence rating. The transition from basic DDoS (2009) to Bitcoin’s sophisticated architecture (2009) represents a significant leap that usually leaves a “paper trail” in intelligence circles which has not yet been publicly declassified.
Cryptocurrency Community & Cypherpunks Perspective
This analysis examines the “Bitcoin Origin Probability Analysis: North Korea vs. Alternative Theories” through the lens of the Cryptocurrency Community and Cypherpunks.
To a Cypherpunk, Bitcoin is not merely a financial asset but a realization of decades of cryptographic activism aimed at preserving individual privacy and undermining state monopolies on money. The suggestion that a totalitarian state—the antithesis of the Cypherpunk ethos—created the protocol is a provocative hypothesis that challenges the community’s foundational narrative.
1. Key Considerations: The Cypherpunk Critique
A. The “Immaculate Conception” vs. State Strategy The community views Bitcoin’s launch as an “immaculate conception”—a neutral, leaderless emergence. The analysis’s focus on North Korea’s (NK) “strategic alignment” ignores the cultural and intellectual lineage of Bitcoin. Bitcoin was the culmination of 20 years of failures on the Cypherpunk mailing lists (e.g., e-gold, b-money, Bit Gold). For NK to have authored the whitepaper, they would have needed to not only master C++ and ECC cryptography but also deeply inhabit the specific philosophical nuances of the 1990s/2000s Cypherpunk discourse. To the community, the “Technical Capability” update (-15%) in the subject analysis is likely an underestimate of the gap.
B. The Fallacy of the “$100B Silence Paradox” The analysis posits that no rational individual would leave $100B untouched. From a Cypherpunk perspective, this is a misunderstanding of Satoshi’s Game Theory.
- The Ultimate OPSEC: Moving those coins would provide a “trail of breadcrumbs” (metadata, exchange touchpoints) that would lead to Satoshi’s doorstep.
- The Martyrdom Principle: Satoshi likely understood that for Bitcoin to be truly decentralized, the creator had to disappear. The “silence” isn’t a paradox; it is the final, necessary component of the protocol’s security.
C. Code as Speech and Ideology The Bitcoin code contains specific choices—like the 21 million cap and the 10-minute block time—that reflect Austrian Economics and libertarian ideals. While the analysis suggests “Juche” doctrine fits, Cypherpunks would argue that a state-created Bitcoin would have likely included a “state key” or a way to inflate the supply to fund the regime. The absence of any “backdoor” in an open-source project scrutinized for 15 years strongly suggests the creator(s) valued the system’s integrity over the state’s utility.
2. Risks to the Ecosystem
- Regulatory Weaponization: The highest risk of the “NK Theory” is its utility for hostile regulators. If Bitcoin is successfully branded as a “North Korean State Project,” it provides the political cover needed for Western governments to ban self-custody or blackhole mining operations under the guise of “National Security” and “Anti-Terrorism.”
- Narrative Contagion: The Bayesian analysis, while logically structured, relies on “Strategic Alignment” (a subjective metric). If this narrative gains mainstream traction, it could deter institutional adoption and cause a “hard fork” in public perception—viewing Bitcoin as a weapon rather than a tool for freedom.
- The “Patoshi” Misinterpretation: The analysis uses the Patoshi pattern as evidence of “institutional-level” mining. The community generally interprets this as Satoshi ensuring the network didn’t suffer a 51% attack in its infancy—a protective “parental” act, not necessarily a state-level operation.
3. Opportunities for the Community
- Doubling Down on Open Source: This analysis highlights the need for even more rigorous “Blockchain Archaeology.” By proving the evolution of the code from earlier Cypherpunk projects, the community can further distance Bitcoin from the “State Actor” theory.
- Refining the “Satoshi” Mythos: The community can use the “Silence Paradox” to reinforce the value of anonymity. Satoshi’s restraint is the ultimate proof-of-work for the ethos of decentralization.
- Focus on Verifiable Evidence: The analysis correctly notes that “Satoshi moving coins” would shift probabilities. The community should continue to monitor the Genesis-era wallets as the ultimate “truth machine” that overrides any circumstantial Bayesian modeling.
4. Specific Insights & Recommendations
- The “Missing Link” Problem: The NK theory lacks a “missing link” between the Hermit Kingdom and the Western Cypherpunk mailing lists of the 90s. Recommendation: Researchers should look for evidence of NK intelligence officers participating in early cryptographic forums under aliases, rather than just looking at “strategic alignment.”
- The “Team” Theory is Undervalued: The analysis gives the “Western Team” only 20%. From a technical standpoint, the synthesis of disparate fields (game theory, distributed systems, p2p networking, and cryptography) suggests a collaborative effort (e.g., Finney, Szabo, and Back) is more likely than a state actor replicating that specific “vibe” and expertise in isolation.
- The “State Actor” Paradox: If NK created Bitcoin to undermine the USD, why would they then spend the last decade hacking other people’s Bitcoin? If they held 1.1 million BTC, their primary goal should be the success and stability of the network, not its destabilization through high-profile thefts (Lazarus Group) which invite regulatory crackdowns.
5. Final Analysis Rating
Confidence Score: 0.85 Reasoning: The analysis of the community’s perspective is grounded in the historical values of the Cypherpunk movement and the technical realities of the Bitcoin protocol. The skepticism toward state-actor theories is a well-documented and logical stance within this specific demographic. However, the 0.15 uncertainty accounts for the fact that in the world of high-level intelligence and cryptography, “truth” is often stranger than “ethos.”
Financial Regulators & Institutional Investors Perspective
This analysis examines the “Bitcoin Origin Probability Analysis” through the lens of Financial Regulators (SEC, CFTC, FATF, OFAC) and Institutional Investors (Hedge Funds, Asset Managers, Pension Funds).
For these stakeholders, the identity of Satoshi Nakamoto is not a matter of historical curiosity; it is a fundamental existential risk factor and a compliance mandate.
1. Regulatory Perspective: The Compliance and National Security Nightmare
From a regulatory standpoint, the hypothesis that North Korea (DPRK) created Bitcoin (45% probability) shifts the asset from a “decentralized commodity” to a potential state-sponsored tool for sanctions evasion and asymmetric financial warfare.
- Sanctions and OFAC Risk: If the DPRK is the creator, the ~1.1 million BTC in the “Satoshi wallets” are technically assets belonging to a Specially Designated National (SDN). For regulators, this creates a “poisoned well” scenario. If a state actor created the protocol to undermine the USD, every transaction on the network could theoretically be viewed as interacting with a system designed for illicit purposes.
- Anti-Money Laundering (AML) / Counter-Terrorism Financing (CTF): Regulators would have to reconsider the “immutability” of Bitcoin. If the creator is a hostile state, the pressure to implement protocol-level censorship or “blacklisting” of UTXOs (Unspent Transaction Outputs) would move from a theoretical debate to a national security requirement.
- Market Integrity: The “Patoshi Pattern” mining suggests a single entity controls a massive portion of the supply. Regulators view this as a “concentration risk” that facilitates market manipulation. If that entity is a rogue state, the risk is not just financial, but geopolitical.
2. Institutional Investor Perspective: The Fiduciary and Tail-Risk Dilemma
Institutional investors operate on the “Rational Actor” model. The analysis’s highlight of the “$100 Billion Silence Paradox” is particularly resonant here.
- The “Sword of Damocles” Risk: Institutional mandates require the assessment of “tail risks.” The 1.1 million BTC held by Satoshi represents roughly 5% of the total supply. If an individual (Szabo/Finney) held this, the risk is “market dump.” If the DPRK holds it, the risk is “geopolitical ransom” or “strategic collapse.” An institutional investor cannot easily justify a long position if there is a 45% chance the founder is a sanctioned regime that could “weaponize” its holdings to crash the price at a politically opportune moment.
- Fiduciary Duty and Reputational Risk: Asset managers (e.g., BlackRock, Fidelity) face immense reputational risk. If the NK theory were proven, “Bitcoin” could become synonymous with “funding nuclear proliferation” in the eyes of ESG-conscious LPs (Limited Partners) and the general public.
- The “Clean Origin” Thesis: Institutions have largely bought into the “Cypherpunk/Grassroots” narrative. This analysis challenges that “immaculate conception” theory. If the origin is “dirty,” the asset’s “Digital Gold” status is compromised, as gold’s value is independent of its discoverer, whereas a digital protocol’s value is partially tied to its governance and intent.
3. Key Risks Identified
- Regulatory Reclassification: A shift in the “NK Probability” could lead to Bitcoin being reclassified as a “security” or a “sanctioned technology,” making it illegal for US/EU institutions to hold.
- Liquidity Shock: If the Satoshi wallets ever move, and the movement is linked to DPRK-associated mixers (like Tornado Cash or Sinbad), the resulting liquidity exit by institutions would be instantaneous and catastrophic for the price.
- Protocol Forking: To “sanitize” the network, the community might be forced to fork Bitcoin to invalidate the Satoshi coins. This would create a “Civil War” within the ecosystem, destroying the “store of value” proposition.
4. Strategic Recommendations
For Regulators:
- Enhanced Forensic Funding: Increase support for “Blockchain Archaeology” to identify if early mining nodes share signatures with known DPRK cyber-operatives (Lazarus Group).
- Contingency Planning: Develop a framework for how to handle “State-Created Decentralized Assets.” Current laws (like the BSA) are ill-equipped for a scenario where the “issuer” is a ghost state.
For Institutional Investors:
- Scenario Analysis: Incorporate the “NK Origin” as a high-impact, low-to-medium probability event in risk models.
- Custody Diversification: Ensure that custody providers have “blacklisting” capabilities that can react in real-time to movements from the Satoshi-era wallets.
- Due Diligence: Move beyond stylometric analysis (which favors individuals) and look at “Operational Security” patterns. The analysis correctly notes that 14 years of silence is more consistent with state-level OPSEC than individual discipline.
5. Analyst Insight: The “Institutional Preference” Bias
The analysis concludes that “conventional wisdom favoring individual creators appears inconsistent with available evidence.” For the financial sector, this is a warning against Narrative Risk. Institutions often prefer the “Individual Genius” story because it is marketable and fits the Silicon Valley venture model. However, the “State Actor” theory, while uncomfortable, explains the technical sophistication and the lack of a “profit-taking” motive far better.
Confidence Rating: 0.85 Reasoning: The Bayesian framework provided is robust and aligns with how intelligence and high-level risk assessments are conducted. While the 45% figure is an estimate, the logic regarding the “100B Silence Paradox” and “Strategic Alignment” is highly persuasive from a risk-management perspective. The uncertainty (0.15) remains because, in the absence of a private key signature, all evidence remains circumstantial.
Academic & Technical Researchers Perspective
This analysis evaluates the “Bitcoin Origin Probability Analysis” from the perspective of Academic and Technical Researchers. Researchers in cryptography, computer science, and forensic linguistics prioritize empirical evidence, peer-reviewed methodology, and the falsifiability of hypotheses.
1. Academic & Technical Critique of the Methodology
From a research standpoint, the use of Bayesian Inference is a commendable attempt to quantify a qualitative mystery. However, a researcher would identify several “soft” points in the application of this framework:
- Subjectivity of Priors and Updates: The “Base Priors” (e.g., 5% for NK vs. 20% for Szabo) are heuristic estimates rather than derived from a statistical distribution of historical state-sponsored vs. individual innovations. In a formal paper, these would require a more robust “Prior Elicitation” process.
- The “Capability Gap” Paradox: The analysis correctly identifies the 2008-2009 NK technical limitations (-15% update). From a computer science perspective, this is the most significant hurdle. The creation of Bitcoin required not just “hacking” skills, but a profound synthesis of game theory, elliptic curve cryptography, and peer-to-peer networking. The leap from basic DDoS (2009) to inventing the Nakamoto Consensus is a non-linear evolution that rarely occurs in isolated state labs without a visible academic trail.
- Stylometric Validity: The analysis mentions stylometry but notes its limitations. Researchers would emphasize that stylometry is most effective with large, controlled corpora. The “Satoshi” corpus is relatively small, and the possibility of “adversarial stylometry” (writing in a different style to mask identity) is a high-probability confounding variable for state actors.
2. Key Considerations
- Blockchain Archaeology: Researchers would focus on the “Patoshi Pattern” and the early source code (pre-v0.1). The code’s “academic” vs. “industrial” style is a key data point. Early Bitcoin code was functional but “messy” in ways that suggest a brilliant but perhaps non-standardized developer—often a hallmark of a lone genius or a small, informal group rather than a state-sanctioned engineering team.
- The $100B Silence Paradox: This is a significant behavioral economics data point. For an individual, the silence is irrational (unless deceased). For a state actor (NK), the silence is a strategic necessity. However, a researcher would ask: If NK owns 1.1 million BTC, why have they spent the last decade risking international exposure to steal much smaller amounts from exchanges? This “Economic Inconsistency” is a major counter-argument to the NK theory.
- Temporal Alignment: The 2009 NK currency reform (revaluation of the won) provides a strong motive, but academic research requires means and opportunity. The timeline between the whitepaper (Oct 2008) and the NK currency crisis (Nov 2009) suggests the project was well underway before the specific “desperation” event occurred.
3. Risks and Opportunities
Risks:
- Post-hoc Ergo Propter Hoc: There is a risk of assuming that because NK is currently the most sophisticated crypto-thief, they must have created the medium. This is a common logical fallacy in intelligence analysis.
- Underestimating the Cypherpunk Ecosystem: The analysis may undervalue the decades of “prior art” (Hashcash, B-money, Bit Gold) that existed in the Western academic/activist mailing lists, which provided a much more fertile “evolutionary soup” for Bitcoin than a closed state environment.
Opportunities:
- Network Latency Analysis: Research into the early nodes’ IP addresses and broadcast times (if recoverable from old logs) could provide geographic “heat maps” of the initial network.
- Formal Verification of the “Team” Theory: Using advanced AI to detect “code signatures” from multiple authors within the original v0.1 source code could confirm or debunk the “Small Team” hypothesis.
4. Specific Recommendations for Further Study
- Comparative Capability Audit: Conduct a deep-dive technical audit of NK’s 2008-2009 malware (e.g., the “MyDoom” variants used in 2009) against the Bitcoin source code to see if there are overlapping libraries, coding conventions, or architectural philosophies.
- Incentive Modeling: Develop a game-theoretic model to explain why a state actor would leave $100B in “clean” founder coins untouched while aggressively pursuing “dirty” coins through hacks that incur high diplomatic and technical costs.
- Linguistic Expansion: Expand stylometric analysis to include translated works of prominent NK computer scientists from the Kim Chaek University of Technology to see if “Korean-influenced English” patterns match the whitepaper.
5. Final Insights
The analysis correctly identifies that the “Individual Creator” theory is failing the “Rational Actor” test due to the $100B silence. However, the “NK State” theory struggles with the “Technical Genesis” test.
The most academically plausible “Middle Path” is a Hybrid Theory: A Western-educated individual or small group (possibly with ideological ties or under duress) working with state resources. This resolves the capability gap while explaining the operational security and the lack of movement in the genesis coins.
Confidence in Analysis: 0.85 Reasoning: The Bayesian framework is sound for hypothesis generation, and the technical critiques provided here are based on established principles of software forensics and behavioral economics. The remaining 0.15 uncertainty stems from the “Black Swan” nature of Satoshi’s identity—any theory could be upended by a single cryptographic proof (a signed message from a Genesis block).
Synthesis
This synthesis integrates four distinct perspectives—National Security, Cypherpunk/Community, Financial/Regulatory, and Academic/Technical—to evaluate the probability that North Korea (DPRK) or a similar state actor created Bitcoin.
1. Common Themes and Areas of Agreement
- The “Silence Paradox” as a Primary Driver: All perspectives agree that the 14-year dormancy of the ~1.1 million BTC in the “Satoshi wallets” (valued at ~$100B) is the strongest evidence against the “Individual Genius” theory. While Cypherpunks view this as “Martyrdom for Decentralization,” the other three perspectives see it as a hallmark of state-level Operational Security (OPSEC) or a “Strategic Reserve” that an individual would find psychologically and practically impossible to maintain.
- Strategic Alignment with DPRK Interests: There is a consensus that Bitcoin serves the DPRK’s “Juche” doctrine of self-reliance. It provides a censorship-resistant rail for sanctions evasion and asymmetric financial warfare, aligning perfectly with the regime’s 2009 currency crisis and its need for non-sovereign hard currency.
- The “Patoshi” Concentration Risk: All stakeholders recognize the “Patoshi Pattern” (the dominant early miner) as a significant risk. Whether viewed as a “Parental Protector” (Cypherpunks) or a “Financial Weapon of Mass Disruption” (NS&I/Regulators), the concentration of 5% of the total supply in a single, silent entity is a systemic “Sword of Damocles.”
- The Utility of Bayesian Analysis: There is general agreement that traditional stylometry (linguistic analysis) is insufficient. A Bayesian framework that incorporates behavioral economics and strategic intent provides a more robust, albeit still probabilistic, model for attribution.
2. Key Conflicts and Tensions
- Ideology vs. Utility: The Cypherpunk perspective argues that Bitcoin’s “DNA”—Austrian economics and libertarian ideals—is fundamentally incompatible with a totalitarian state. Conversely, the NS&I and Academic perspectives suggest that state actors frequently co-opt ideologies or use “cut-outs” (foreign experts/front companies) to achieve utilitarian goals, rendering the “vibe” of the code a potentially deceptive signal.
- The “Lazarus Paradox”: A major point of tension is the “Economic Inconsistency” argument. Academics and Cypherpunks ask: If the DPRK holds $100B in clean BTC, why do they risk international exposure to steal much smaller amounts via the Lazarus Group? The NS&I response is that the Satoshi coins are a “strategic deterrent” or “nuclear option” that cannot be moved without destroying the asset’s legitimacy, whereas hacks provide “disposable” operational liquidity.
- Technical Capability Gap: Technical researchers and Cypherpunks emphasize that the leap from the DPRK’s known 2009 capabilities (basic DDoS attacks) to the sophisticated synthesis of the “Nakamoto Consensus” is nearly insurmountable. NS&I analysts counter that talent procurement (coercion or hiring of Western experts) could bridge this gap, a tactic the DPRK has successfully used in its nuclear program.
3. Overall Consensus Assessment
Consensus Level: 0.75 (High)
There is a strong emerging consensus that the “Individual Creator” theory is failing the “Rational Actor” test, primarily due to the Silence Paradox. While the “DPRK Theory” is not yet proven, it has moved from a fringe conspiracy to a high-impact, medium-probability hypothesis that demands serious institutional attention. The most widely accepted “middle path” across all perspectives is a Hybrid Theory: a small group of Western-educated experts (possibly Cypherpunks) working under the aegis, funding, or coercion of a state actor.
4. Unified Recommendations
To address the risks and uncertainties identified across all sectors, the following actions are recommended:
- Advanced Blockchain Archaeology: Move beyond linguistic analysis to “Technical Forensics.” This includes cross-referencing early mining node latency and IP traffic (where recoverable) with known state-actor digital footprints from 2008–2009.
- Formal National Intelligence Estimate (NIE): The intelligence community should conduct a formal attribution review. If the probability of state-origin exceeds a certain threshold, Bitcoin must be re-evaluated not just as a commodity, but as a dual-use technology with national security implications.
- Institutional “Tail-Risk” Modeling: Financial institutions and regulators should incorporate the “State-Actor Origin” as a high-impact risk scenario. This includes developing contingency plans for a “Protocol Fork” to invalidate the Satoshi wallets should they ever be definitively linked to a sanctioned regime.
- Monitoring the “Dead Man’s Switch”: Any movement in the Genesis-era wallets should be treated as a Tier-1 geopolitical event. The “truth machine” of the blockchain remains the only definitive way to resolve the mystery; until then, the asset’s origin remains a fundamental “known unknown” in the global financial system.
Final Conclusion
The synthesis suggests that while the “immaculate conception” of Bitcoin remains the preferred cultural narrative, the strategic, behavioral, and financial evidence increasingly points toward an institutional or state-backed origin. The “Silence Paradox” is the pivot point: it is either the greatest act of individual altruism in history or the most disciplined state intelligence operation of the 21st century. Given the stakes, the latter must be treated as a credible and actionable risk.
